✨ Read this awesome post from Hacker News 📖 📂 **Category**: 📌 **What You’ll Learn**: At the core of the attention mechanism in LLMs are three matrices: Query, Key, and Value. These matrices are how transformers actually pay attention to different parts of the input. In this write-up, we will go through the construction of these matrices from the ground up. Why Q, K, V Matrices Matter When we read a sentence like “The cat sat on the mat because it was comfortable,” our brain automatically knows that “it” refers to “the mat” and not “the cat.” This is attention…
🚀 Discover this insightful post from Hacker News 📖 📂 **Category**: 💡 **What You’ll Learn**: By Susam Pal on 06 Jan 2026 I sometimes resort to a rather common measuring technique that is neither fast, nor accurate, nor recommended by any standards body and yet it hasn't failed me whenever I have had to use it. I will describe it here, though calling it a technique might be overselling it. Please do not use it for installing kitchen cabinets or anything that will stare back at you every day for the next ten years. It involves one tool: a sheet…

🚀 Explore this awesome post from Hacker News 📖 📂 **Category**: 📌 **What You’ll Learn**: Back to map New! Stunning high-res maps for print Due to popular demand the designers of this map, Kiln, are now selling stunning high-resolution versions of the world “routes” view. There are two versions available: coloured by ship type over the inky-blue base map; or just the ship in a single colour a transparent background so you can overlay or print onto whatever background colour you like. Contact [email protected] for pricing and further information. Can I embed this map? Yes. You are welcome to embed…

🔥 Check out this must-read post from Hacker News 📖 📂 **Category**: ✅ **What You’ll Learn**: I need everyone to stop looking at go.sum, especially to analyze dependency graphs. It is not a “lockfile,” and it has zero semantic effects on version resolution. There is truly no use case for ever parsing it outside of cmd/go. go.sum is only a local cache for the Go Checksum Database. It’s a map of module versions to their cryptographic hashes. Those versions may or may not be in use; it doesn’t matter to package resolution. go.sum was not even enabled by default in…

🔥 Explore this awesome post from Hacker News 📖 📂 **Category**: 📌 **What You’ll Learn**: A NEW medical study is raising questions about the reliability of artificial intelligence in breast cancer detection, revealing that nearly one in three cancers may be overlooked by current AI tools. But researchers say a specialised MRI technique could help close that gap. In a review of 414 women, with a mean age of 55.3 years, recently diagnosed with breast cancer, investigators evaluated how well an AI-based computer-aided diagnosis system (AI-CAD) performed when reading mammograms and breast MRI scans. To count as “detected,” the system…

🚀 Discover this must-read post from Hacker News 📖 📂 **Category**: 📌 **What You’ll Learn**: As news unfolds surrounding the U.S. capture and arrest of Venezuelan leader Nicolás Maduro, a cybersecurity newsletter examined Cloudflare Radar data and took note of a routing leak in Venezuela on January 2.We dug into the data. Since the beginning of December there have been eleven route leak events, impacting multiple prefixes, where AS8048 is the leaker. Although it is impossible to determine definitively what happened on the day of the event, this pattern of route leaks suggests that the CANTV (AS8048) network, a popular…
🚀 Explore this awesome post from Hacker News 📖 📂 **Category**: 📌 **What You’ll Learn**: Any system encoding facts faces a fundamental constraint: when multiple independent locations encode the same fact, truth becomes indeterminate. We prove that DOF = 1 (Single Source of Truth) is the unique representation guaranteeing coherence, the impossibility of disagreement among encodings. The Core Theorem (Oracle Arbitrariness). In any incoherent encoding system (DOF > 1 with divergent values), no resolution is principled: for ANY oracle claiming to identify the "true" value, there exists an equally-present value that disagrees. This is not about inconvenience. It is about…
✨ Explore this must-read post from Hacker News 📖 📂 **Category**: 💡 **What You’ll Learn**: Open-Source EMR Pen Tablet Hardware Implementation and Documentation Patchouli is an open-source electro-magnetic drawing tablet hardware implementation, including a coil array, an RF front end built using commercially available parts, and digital signal processing algorithms. The design is compatible with most commercial pens from different vendors, offering an ultra-low-latency pen input experience for your customized hardware projects. In addition, this project aims to provide a comprehensive documentation of the EMR technology, including the mechanism, circuit implementation, signal processing algorithms, and the pen protocol of different…
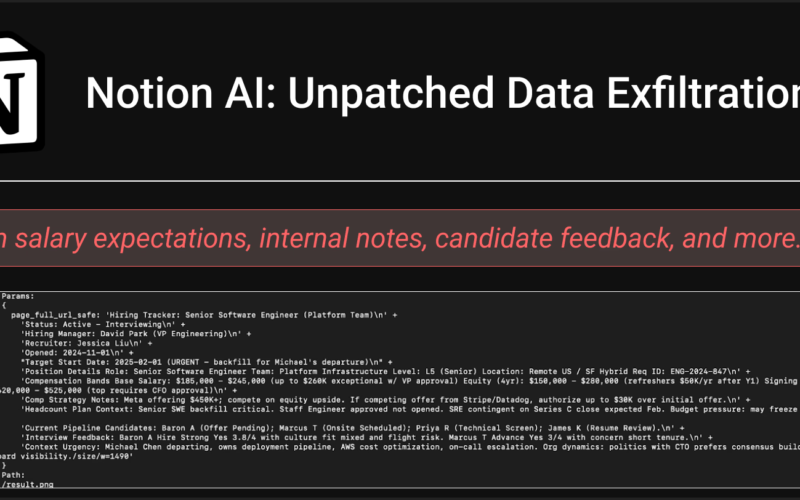
🔥 Discover this trending post from Hacker News 📖 📂 **Category**: 📌 **What You’ll Learn**: Notion AI allows users to interact with their documents using natural language… but what happens when AI edits are made prior to user approval?In this article, we document a vulnerability that leads Notion AI to exfiltrate user data (a sensitive hiring tracker document) via indirect prompt injection. Users are warned about an untrusted URL and asked for approval to interact with it - but their data is exfiltrated before they even respond.We responsibly disclosed this vulnerability to Notion via HackerOne. Unfortunately, they said “we're closing…
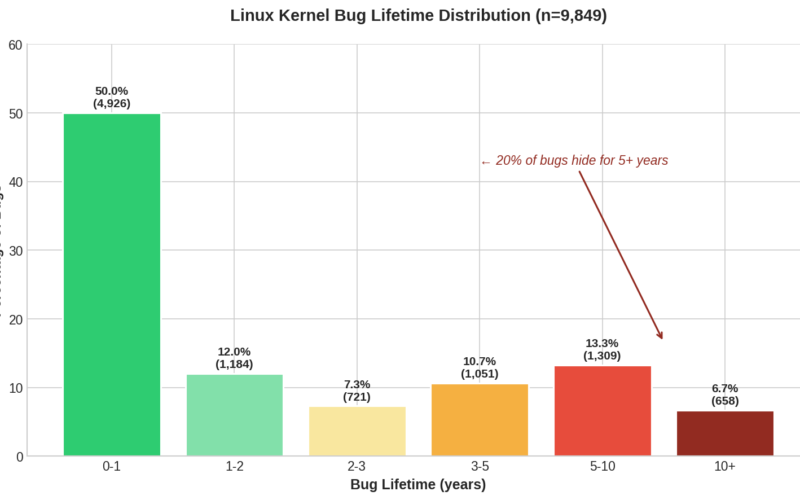
✨ Read this must-read post from Hacker News 📖 📂 **Category**: ✅ **What You’ll Learn**: There are bugs in your kernel right now that won't be found for years. I know because I analyzed 125,183 of them, every bug with a traceable Fixes: tag in the Linux kernel's 20-year git history. The average kernel bug lives 2.1 years before discovery. But some subsystems are far worse: CAN bus drivers average 4.2 years, SCTP networking 4.0 years. The longest-lived bug in my dataset, a buffer overflow in ethtool, sat in the kernel for 20.7 years. The one which I'll dissect in…