🚀 Read this trending post from Hacker News 📖 📂 Category: 📌 Key idea: The PlayStation 5’s ROM keys have allegedly been leaked, meaning anyone who can get their hands on the hex strings now has the hardware code that will allow jailbreakers to try decrypting and analyzing the console’s bootloader. According to The Cybersec Guru, this is an unpatchable problem for Sony, because these keys cannot be changed and are burned directly in the APU. The only way that the company can invalidate the leaked codes is to replace the chips on yet-to-be-manufactured units, meaning consoles that are already…

🔥 Explore this must-read post from Hacker News 📖 📂 Category: 📌 Main takeaway: A few years ago, I was going a little mad.Materially, my life was comfortable. My partner and I had just bought a house. I was doing okay in a freelance writing career. And we were living the sort of middle class-ish lifestyle where we could afford multiple foreign holidays a year.But there was something I found disturbing. I didn’t have any reason to ever leave the house.That’s not much of an exaggeration. Through a combination of luck and circumstance, I’d landed in a work-from-home career where…

💥 Read this trending post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: Tesla-compiled estimates show Q4 deliveries expected to fall 15% from last yearA Tesla-compiled average of analyst estimates pegs fourth-quarter deliveries at 422,850, which would mark a 15% slump from the 495,570 the company delivered in the same quarter last year, if realized. The full-year estimate of 1.6 million vehicles would represent an 8% decline from 2024 and the second annual decline for the EV company. The estimates are notably lower than the consensus estimates compiled by Bloomberg and FactSet, which have been declining over…
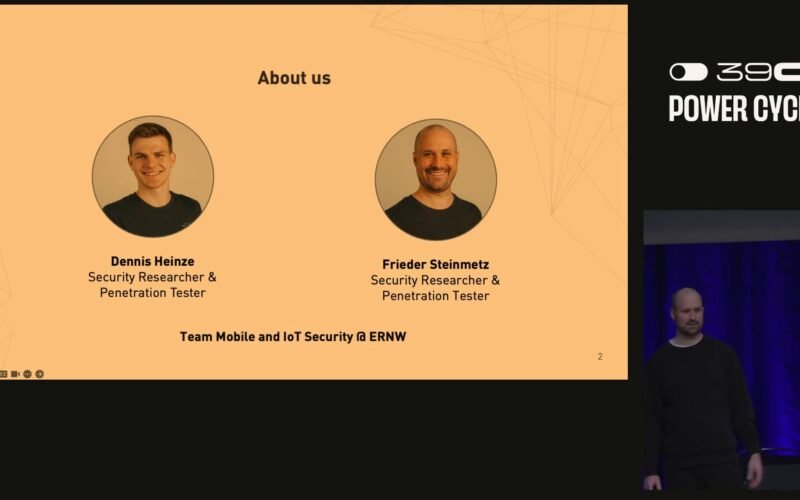
💥 Explore this awesome post from Hacker News 📖 📂 Category: 💡 Key idea: Bluetooth Headphone Jacking: A Key to Your Phone - media.ccc.de Dennis Heinze and Frieder Steinmetz One Security Playlists: '39c3' videos starting here / audio Bluetooth headphones and earbuds are everywhere, and we were wondering what attackers could abuse them for. Sure, they can probably do things like finding out what the person is currently listening to. But what else? During our research we discovered three vulnerabilities (CVE-2025-20700, CVE-2025-20701, CVE-2025-20702) in popular Bluetooth audio chips developed by Airoha. These chips are used by many popular device manufacturers…

🔥 Explore this trending post from Hacker News 📖 📂 Category: 📌 Main takeaway: Typically when receiving any review hardware preloaded with Microsoft Windows I tend to run some Windows vs. Linux benchmarks just as a sanity test plus it still seems to generate a fair amount of interest even though the outcome is almost always the same: Linux having a hefty performance advantage over Windows especially in the more demanding creator-type workloads. As an unexpected twist and time consuming puzzle the past two months, when recently testing out the Lenovo ThinkPad P1 Gen 8 it's faster for numerous workloads…

🔥 Check out this awesome post from Hacker News 📖 📂 Category: ✅ Key idea: An Australian boatbuilder has launched what it describes as the world’s largest battery-power ship, describing it as a “a giant leap forward in sustainable shipping” and the “most important” project it has ever done.Incat, a manufacturer based in Tasmania, constructed the ship – called Hull 096 – after being contracted by the South American ferry operator Buquebus to build a vessel to run between the Argentinian capital, Buenos Aires, and Uruguay.Launching the ship in Hobart on Friday, the company said it would operate entirely on…
🔥 Check out this trending post from Hacker News 📖 📂 Category: ✅ Key idea: Note: this is a "script" for a podcast that I recently recorded, as such it's more conversational and less technical than the usual content of this blog. Not a single code block in sight... Prologue Imagine you wake up one night to find out that production is crashing. It takes you a while to unearth the root cause. It turns out to be a null pointer exception deep inside a service. It crashed the whole system. How did it get there? Where did it come…
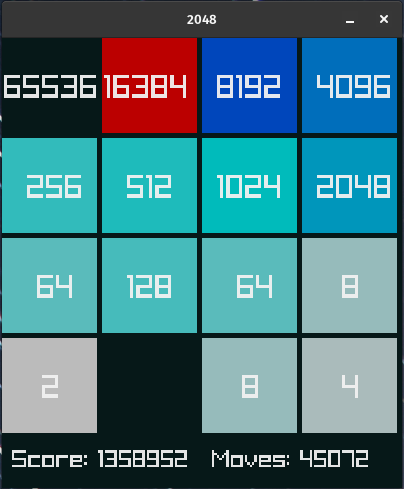
🔥 Explore this must-read post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: Training gaming agents is an addictive game. A game of sleepless nights, grinds, explorations, sweeps, and prayers. PufferLib allows anyone with a gaming computer to play the RL game, but getting from “pretty good” to “superhuman” requires tweaking every lever, repeatedly. This is the story of how I trained agents that beat massive (few-TB) search-based solutions on 2048 using a 15MB policy trained for 75 minutes and discovered that bugs can be features in Tetris. TLDR? PufferLib, Pareto sweeps, and curriculum learning. Speed and…
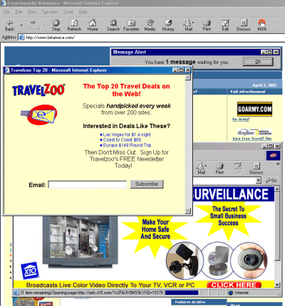
🔥 Discover this must-read post from Hacker News 📖 📂 Category: 💡 Key idea: If you were an Internet user for a few years on either side of the turn of the millennium, you will remember pop-up advertisements. Two pop-up ad windows displayed over the legitimate website in the background. (Screenshot from HowStuffWorks. April, 2002.) A poorly-considered web browser feature allowed website authors to open new browser windows on your computer containing some other website. This was quickly abused to show ads to users. You’d visit a website and receive an ad that covered up the contents you were there…
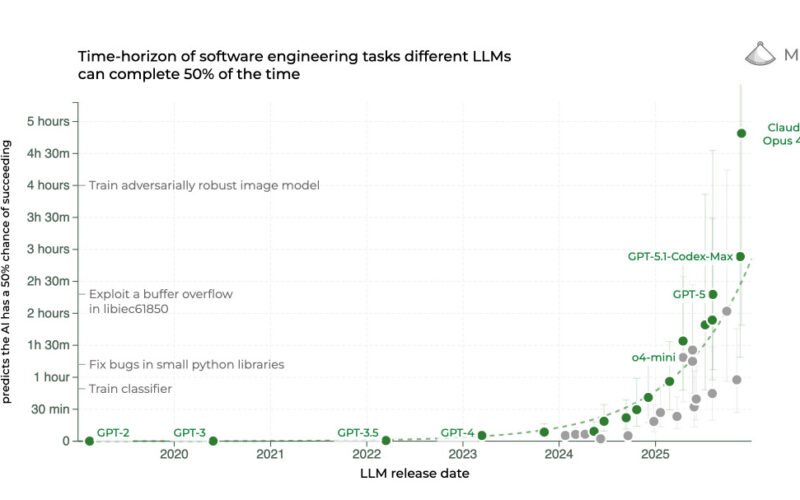
🚀 Check out this awesome post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: 2025: The year in LLMs 31st December 2025 This is the third in my annual series reviewing everything that happened in the LLM space over the past 12 months. For previous years see Stuff we figured out about AI in 2023 and Things we learned about LLMs in 2024. It’s been a year filled with a lot of different trends. The year of “reasoning” OpenAI kicked off the “reasoning” aka inference-scaling aka Reinforcement Learning from Verifiable Rewards (RLVR) revolution in September 2024 with…

