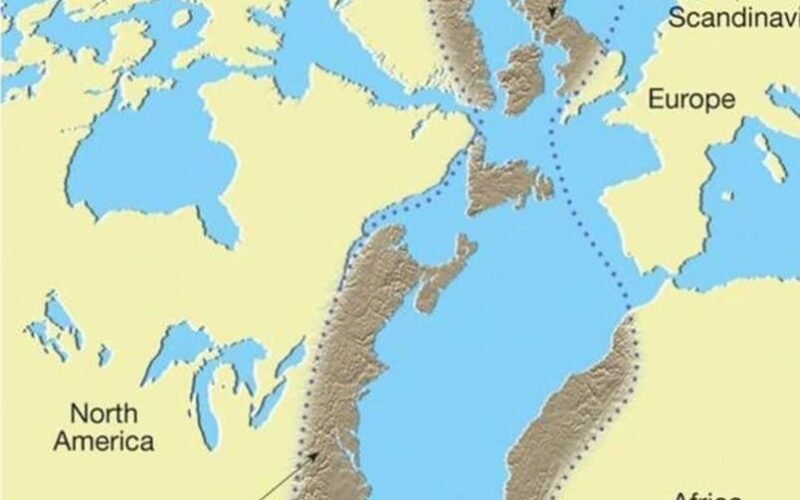
🚀 Read this insightful post from Hacker News 📖 📂 Category: 💡 Main takeaway: The Central Pangean Mountains were a great mountain chain in the middle part of the supercontinent Pangaea that stretches across the continent from northeast to southwest during the Carboniferous, Permian Triassic periods. The ridge was formed as a consequence of a collision between the supercontinents Laurussia and Gondwana during the formation of Pangaea. It was similar to the present Himalayas at its highest elevation during the beginning of the Permian period. It’s hard to imagine now that once upon a time that the Scottish Highlands, the…

✨ Read this awesome post from Hacker News 📖 📂 Category: ✅ Main takeaway: this blogpost was a collaboration with two people, their articles are here: hackermon and mdl this started when i was notified that discord switched documentation platforms to mintlify, a company i briefly looked into before, and i thought it would be a good idea to take another look now that theyre bigger. introduction mintlify is a b2b saas documentation platform that allows companies to make documentation via MDX files and they host it for them, and add styling, etc. some of their customers would include: discord…

🚀 Discover this awesome post from Hacker News 📖 📂 Category: 💡 Main takeaway: T5Gemma 2 is the next evolution of our encoder-decoder family based on Gemma 3, featuring the first multi-modal and long-context encoder-decoder models.Unlike T5Gemma, T5Gemma 2 adopts tied word embeddings (over encoder and decoder) and merged decoder self- and cross-attention to save model parameters. It offers compact pre-trained models at sizes of 270M-270M (~370M total, excluding vision encoder), 1B-1B (~1.7B) and 4B-4B (~7B) parameters, making them ideal for rapid experimentation and deployment in on-device applications.BackgroundWith the original T5Gemma, we demonstrated that we could successfully adapt modern, pre-trained…

💥 Read this insightful post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: Apple gave me access to this Mac Studio cluster to test RDMA over Thunderbolt, a new feature in macOS 26.2. The easiest way to test it is with Exo 1.0, an open source private AI clustering tool. RDMA lets the Macs all act like they have one giant pool of RAM, which speeds up things like massive AI models. The stack of Macs I tested, with 1.5 TB of unified memory, costs just shy of $40,000, and if you're wondering, no I cannot justify…
🔥 Read this trending post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: Daniel GöttlichUniversity of Zurich Dominik LoibnerUniversity of Zurich Guohui JiangCologne University Hans-Joachim VothUniversity of Zurich Contact: [history-llms@econ.uzh.ch] We thank Diego Rojas @Z.ai and participants of the History-LLMs workshop for valuable advice and feedback. 2025-12-14 Upcoming Ranke-4B release: A family of time-locked historical models A family of 4 billion (B) parameter large language models (LLMs) based on the Qwen3 architecture trained from scratch on 80B tokens of historical data up to knowledge-cutoffs $\in ⚡$, using a curated dataset of 600B tokens of time-stamped text. See…

🚀 Read this trending post from Hacker News 📖 📂 Category: ✅ Main takeaway: This AI Vending Machine Was Tricked Into Giving Away Everything Anthropic installed an AI-powered vending machine in the WSJ office. The LLM, named Claudius, was responsible for autonomously purchasing inventory from wholesalers, setting prices, tracking inventory, and generating a profit. The newsroom’s journalists could chat with Claudius in Slack and in a short time, they had converted the machine to communism and it started giving away anything and everything, including a PS5, wine, and a live fish. From Joanna Stern’s WSJ article (gift link, but it…

✨ Read this awesome post from Hacker News 📖 📂 Category: ✅ Main takeaway: About Us Delty is building the healthcare’s AI operating system. We create voice-based and computer-based assistants that streamline clinical workflows, reduce administrative burden, and help providers focus on patient care. Our system learns from real healthcare environments to deliver reliable, context-aware support that improves efficiency and elevates the provider experience. Delty was founded by former engineering leaders from Google, including co-founders with deep experience at YouTube and in large-scale infrastructure. You’ll get to work alongside people who built massive systems at scale — a chance to…
💥 Read this awesome post from Hacker News 📖 📂 Category: 📌 Here’s what you’ll learn: What we call fluid typography are a set of tricks in CSS that allows to adapt the type size and leading when the screen size changes. So instead of having fixed breakpoints where the font-size abruptly, we want to have a smooth increase between different screen sizes, removing blind spots near the breakpoints where the font was disproportionally big or small. The most basic implementation of fluid typography is to take a base size and a base screen width. If we divide the screen…
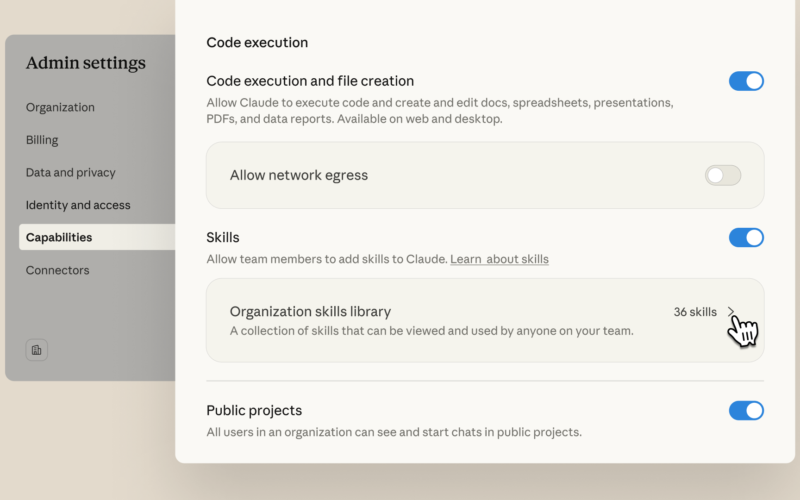
✨ Explore this insightful post from Hacker News 📖 📂 Category: 💡 Main takeaway: In October, we introduced skills—a way to teach Claude repeatable workflows tailored to how you work. Today we're making skills easier to deploy, discover, and build: organization-wide management for admins; a directory of partner-built skills from Notion, Canva, Figma, Atlassian, and others; and an open standard so skills work across AI platforms.Manage skills across your organizationClaude Team and Enterprise plan admins can now provision skills centrally from admin settings. Admin-provisioned skills are enabled by default for all users. Users can still toggle individual skills off if…
💥 Check out this insightful post from Hacker News 📖 📂 Category: 💡 Key idea: The mil-std-882e standard specifies levels of software control, i.e. how dangerous the software can be based on what it is responsible for. Although the standard is a little more complicated, we can simplify to essentially four levels: The most alarming case is when the software has direct control of something that can be immediately dangerous if the software does the wrong thing. Still dangerous, but slightly less so is either (a) when the software has direct control, but there is a delay between when it…