🔥 Discover this insightful post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: Hi HN, we’re Sid and Ritvik, co-founders of Pulse. Pulse is a document extraction system to create LLM-ready text. We built Pulse as we realized that although modern vision language models are very good at producing plausible text, that makes them risky for OCR and data ingestion at scale.When we started working on document extraction, we assumed the same thing many teams do today: foundation models were improving quickly, multi modal systems appeared to read documents well, and for small or clean inputs that…
✨ Read this awesome post from Hacker News 📖 📂 Category: 📌 Main takeaway: Your job is to deliver code you have proven to work 18th December 2025 In all of the debates about the value of AI-assistance in software development there’s one depressing anecdote that I keep on seeing: the junior engineer, empowered by some class of LLM tool, who deposits giant, untested PRs on their coworkers—or open source maintainers—and expects the “code review” process to handle the rest. This is rude, a waste of other people’s time, and is honestly a dereliction of duty as a software developer.…
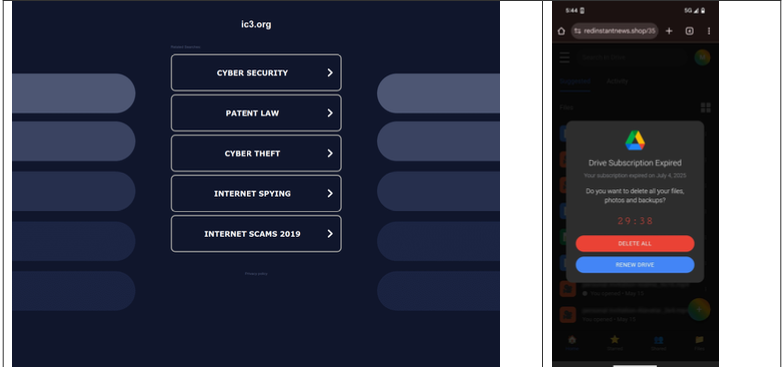
🚀 Read this awesome post from Hacker News 📖 📂 Category: ✅ Main takeaway: Direct navigation — the act of visiting a website by manually typing a domain name in a web browser — has never been riskier: A new study finds the vast majority of “parked” domains — mostly expired or dormant domain names, or common misspellings of popular websites — are now configured to redirect visitors to sites that foist scams and malware. A lookalike domain to the FBI Internet Crime Complaint Center website, returned a non-threatening parking page (left) whereas a mobile user was instantly directed to…
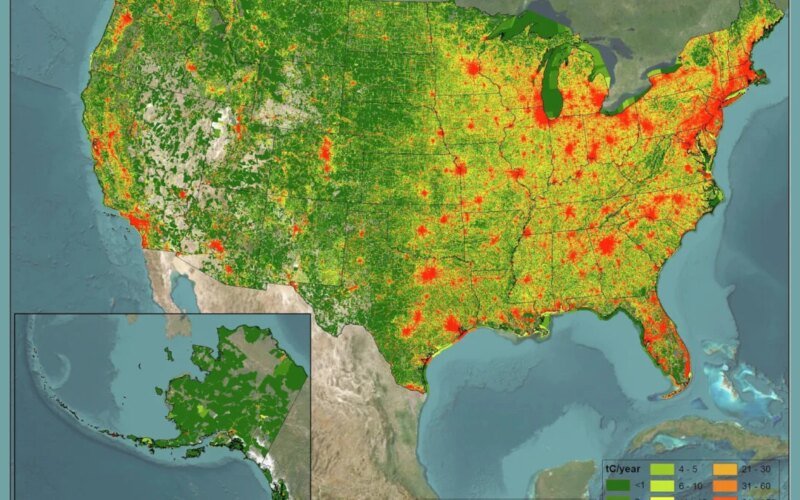
💥 Read this trending post from Hacker News 📖 📂 Category: 💡 Here’s what you’ll learn: When it comes to fighting climate change, you can’t manage what you can’t measure. Under the Trump administration, U.S. efforts to track planet-warming carbon dioxide (CO2) emissions face an existential threat, but that isn’t stopping one team of researchers from producing this essential data. In a study published Wednesday in the journal Nature Scientific Data, the team presented findings from the fourth version of Vulcan, a dataset that captures every source of CO2 emissions from fossil fuel combustion across the United States at an…

💥 Check out this trending post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: Encrypted messaging developers may be considered hostile actors in the UKAn independent review of national security law warns of overreach Encryption repeatedly targeted by UK lawmakers Developers of apps that use end-to-end encryption to protect private communications could be considered hostile actors in the UK.That is the stark warning from Jonathan Hall KC, the government’s Independent Reviewer of State Threats Legislation and Independent Reviewer of Terrorism Legislation, in a new report on national security laws.In his independent review of the Counter-Terrorism and Border…

🔥 Read this trending post from Hacker News 📖 📂 Category: 📌 Here’s what you’ll learn: More than international sanctions, more than its stifling theocracy, more than recent bombardment by Israel and the U.S. — Iran’s greatest current existential crisis is what hydrologists are calling its rapidly approaching “water bankruptcy.” It is a crisis that has a sad origin, they say: the destruction and abandonment of tens of thousands of ancient tunnels for sustainably tapping underground water, known as qanats, that were once the envy of the arid world. But calls for the Iranian government to restore qanats and recharge the…

💥 Explore this trending post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: Business Uploaded by PTReporter on Dec 17, 2025 GitHub update on the postponement of the price increase for GitHub Actions for self-hosted runners to $0.002 per minute. Below is a screenshot of the update shared on X (@github). GitHub had earlier announced in a post we published that it would increase the cost of self-hosted runners from $0.00 (free) to $0.002 per minute, starting March 1, 2026. This increase has been postponed, which means it will not apply until a new decision is made.…

💥 Discover this awesome post from Hacker News 📖 📂 Category: 📌 Here’s what you’ll learn: Electronics biz Vizio may be required by a California court to provide source code for its SmartCast TV software, which is allegedly based on open source code licensed under the GPLv2 and LGPLv2.1. The legal complaint from the Software Freedom Conservancy (SFC) seeks access to the SmartCast source code so that Vizio customers can make changes and improvements to the platform, something that ought to be possible for code distributed under the GPL. On Thursday, California Superior Court Judge Sandy Leal issued a tentative…
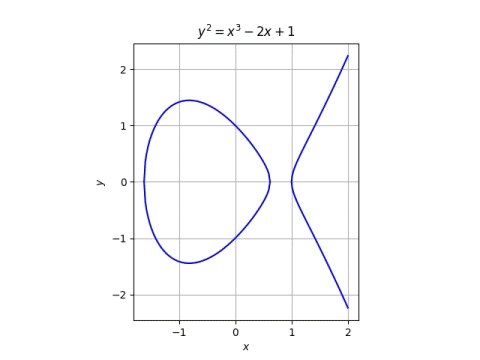
✨ Explore this must-read post from Hacker News 📖 📂 Category: 📌 Key idea: Elliptic curves are pure and applied, concrete and abstract, simple and complex. Elliptic curves have been studied for many years by pure mathematicians with no intention to apply the results to anything outside math itself. And yet elliptic curves have become a critical part of applied cryptography. Elliptic curves are very concrete. There are some subtleties in the definition—more on that in a moment—but they’re essentially the set of points satisfying a simple equation. And yet a lot of extremely abstract mathematics has been developed out…

💥 Explore this trending post from Hacker News 📖 📂 Category: 💡 Key idea: Megan LawtonBusiness reporterAFP via Getty ImagesOne UK study found that 34% of advertised vacancies didn't really existThe phrase "ghost jobs" might sound like something from Halloween, but it refers to the practice of employers advertising vacancies that don't exist.In some cases the positions may have already been filled, but in others the job might not have ever been available.It's a real and continuing problem on both sides of the Atlantic.Up to 22% of jobs advertised online last year were positions listed with no intent to hire,…
