✨ Explore this trending post from Hacker News 📖 📂 Category: 📌 Here’s what you’ll learn: It was yet another day at the office. Our team was internally discussing moving to a different platform analytics solution. Our team was really leaning more towards Posthog. It’s one of the brilliant -I personally believe it’s the best- products on the market. And that’s where the story has begun… We have a somewhat unconventional—some might say non-scalable—approach to vendor selection. Before we seriously consider adopting a product, we give ourselves a strict 24-hour “research window.” Not a marketing review. Not a feature comparison…

🚀 Check out this must-read post from Hacker News 📖 📂 Category: 💡 Main takeaway: Many people think of VisiCalc as the first spreadsheet, and while VisiCalc was the first spreadsheet on the desktop, it’s not actually the first spreadsheet.Ten years before VisiCalc, two engineers at Bell Canada came up with a pretty neat idea. At the time, organizational budgets were created using a program that ran on a mainframe system. If a manager wanted to make a change to the budget model, that might take programmers months to create an updated version.Rene Pardo and Remy Landau discussed the problem…
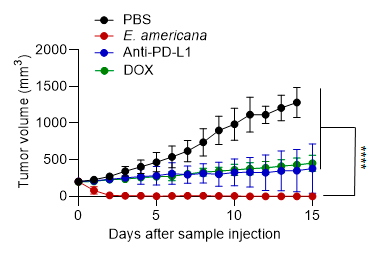
🚀 Discover this awesome post from Hacker News 📖 📂 Category: 💡 Key idea: 【Key Research Achievements】 Demonstration that natural bacteria isolated from amphibian and reptile intestines achieve complete tumor elimination with single administration Combines direct bacterial killing of cancer cells with immune system activation for comprehensive tumor destruction Outperforms existing chemotherapy and immunotherapy with no adverse effects on normal tissues Expected applications across diverse solid tumor types, opening new avenues for cancer treatment 【Research Overview】 A research team of Prof. Eijiro Miyako at the Japan Advanced Institute of Science and Technology (JAIST) has discovered that the bacterium Ewingella americana,…

💥 Read this must-read post from Hacker News 📖 📂 Category: ✅ Main takeaway: Unlawful tracking across apps. It’s no secret that TikTok is rather data hungry. After all, the popular video platform’s algorithm seems to know exactly what content users want to see. However, it’s not well known that TikTok also tracks you while using other apps. A user found out about this unlawful tracking practice through an access request – which showed that e.g. his usage of Grindr was sent to TikTok, likely via the Israeli tracking company AppsFlyer - which allows TikTok to draw conclusions about his…

🔥 Check out this awesome post from Hacker News 📖 📂 Category: 💡 Here’s what you’ll learn: Starting with OBS Studio 32.0.0 a new renderer backend based on Apple's Metal graphics API is available for users to test as an experimental alternative to the existing OpenGL backend on macOS. This marks an important step in OBS Studio's development to adapt one of the modern APIs that deliberately broke with the past to unlock better performance and efficiency gains for end users, but also require fundamental changes to how an application interacts with a GPU. These fundamental changes were necessary to…

🔥 Explore this must-read post from Hacker News 📖 📂 Category: 📌 Main takeaway: In October, the Vanderbilt Policy Accelerator published research showing that companies use loyalty programs to hook consumers, creating a captive audience they can track. Because consumers opt into these programs in the hopes of discounts and rewards, the programs are exempt from many state and federal laws about surveillance. And some companies eagerly abuse that legal opening.Of course, loyalty programs pre-date AI, not to mention the internet itself. But gone are the punch cards of yore. The Vanderbilt report’s lead example is the McDonald’s Monopoly game…

🚀 Discover this trending post from Hacker News 📖 📂 Category: 💡 Key idea: Or: How I learned that “I don’t use Next.js” doesn’t mean your dependencies don’t use Next.js 8:25 AM: The Email I woke up to this beauty from Hetzner: Dear Mr Jake Saunders, We have indications that there was an attack from your server. Please take all necessary measures to avoid this in the future and to solve the issue. We also request that you send a short response to us. This response should contain information about how this could have happened and what you intend to…

💥 Discover this must-read post from Hacker News 📖 📂 Category: ✅ Main takeaway: This summer, as the world gathers to celebrate the FIFA World Cup 2026, fans can play a newly reimagined FIFA football simulation game exclusively on Netflix Games. The game, developed and published by Delphi Interactive, allows Netflix members to experience the emotion and drama of the tournament in its purest, most joyful form — in a format that’s fast to learn, thrilling to master, and built for anyone to jump in. Plus, you can play solo or with friends online: All you need is Netflix and your phone.“The…
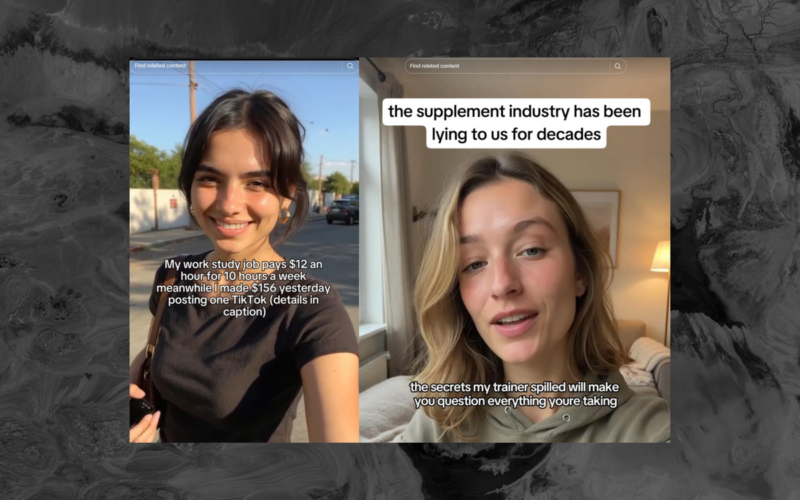
✨ Discover this trending post from Hacker News 📖 📂 Category: 📌 Here’s what you’ll learn: Doublespeed, a startup backed by Andreessen Horowitz (a16z) that uses a phone farm to manage at least hundreds of AI-generated social media accounts and promote products has been hacked. The hack reveals what products the AI-generated accounts are promoting, often without the required disclosure that these are advertisements, and allowed the hacker to take control of more than 1,000 smartphones that power the company. The hacker, who asked for anonymity because he feared retaliation from the company, said he reported the vulnerability to Doublespeed on…
🚀 Check out this insightful post from Hacker News 📖 📂 Category: 📌 Key idea: How SQLite Is Tested Table Of Contents The reliability and robustness of SQLite is achieved in part by thorough and careful testing. As of version 3.42.0 (2023-05-16), the SQLite library consists of approximately 155.8 KSLOC of C code. (KSLOC means thousands of "Source Lines Of Code" or, in other words, lines of code excluding blank lines and comments.) By comparison, the project has 590 times as much test code and test scripts - 92053.1 KSLOC. 1.1. Executive Summary Four independently developed test harnesses 100% branch…

