💥 Discover this must-read post from Hacker News 📖 📂 Category: 💡 Here’s what you’ll learn: In particular, Katzarkov wanted to break the mirror image’s curve count into pieces, then use the mirror symmetry program to show that there was a corresponding way to break up the four-fold’s Hodge structure. He could then work with these pieces of the Hodge structure, rather than the whole thing, to show that four-folds can’t be parameterized. If any one of the pieces couldn’t be mapped to a simple 4D space, he’d have his proof. But this line of reasoning depended on the assumption…
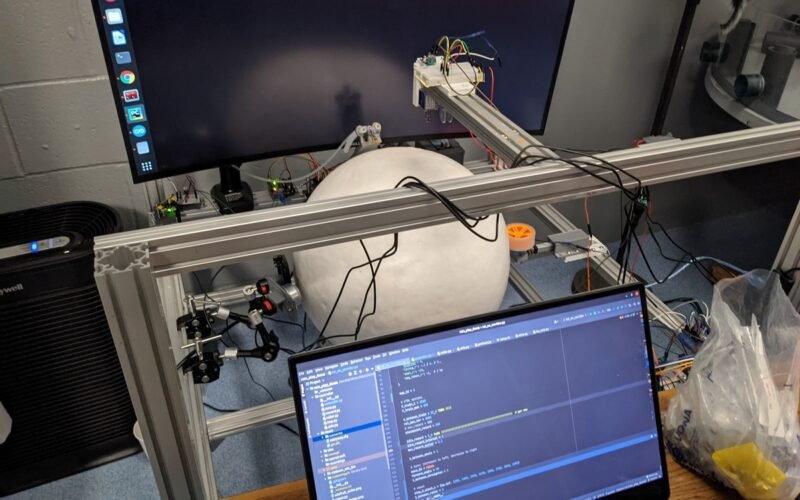
🚀 Read this awesome post from Hacker News 📖 📂 Category: ✅ Main takeaway: Intro We built a complete VR setup from scratch to let rats play DOOM. The system includes a motion-tracked treadmill ball, a panoramic headset, an input trigger, and a reward circuit. All hardware and software components are open sourced, including 3D-printable designs, circuit diagrams, firmware, and control software. The first version (v1) was built in New York by Viktor, who trained rats to walk through a corridor in DOOM using a simpler rig. That version was featured on Vice and PC Gamer. After moving back home,…

🔥 Check out this insightful post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: In late 2022, I had a conversation with a senior engineer on the coming problem of “what to do when AI is writing most of the code”. His opinion, which I found striking at the time, was that engineers would transition from writing mostly “implementation” code, to mostly writing tests and specifications. I remember thinking at the time that this was prescient. With three years of hindsight, it seems like things are trending in a different direction. I thought that the reason that…

💥 Read this must-read post from Hacker News 📖 📂 Category: 📌 Here’s what you’ll learn: Home > Anti-Piracy > Site Blocking > Google has removed dozens of new Sci-Hub domain names from its search results in the United States. Unlike typical DMCA takedowns, the removals were triggered by a dated court order that was not enforced for several years. This appears to be one of the first times Google has deindexed an entire pirate site in the U.S. based on a 'site blocking' style injunction. In 2017, American Chemical Society (ACS), a leading source of academic publications in the…
💥 Check out this awesome post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: This title is an obvious nod toTo encrypt email in 1998 you’d run GnuPG from a terminal, importing the recipient’s public key into your local keyring then copying your email text into a file then encrypting the file for that public key: gpg -e -r alice file. Finally you’d copy the encrypted message into your email client and send it out.In 2025, it’s pretty much the same. In some respects, it’s worse:It feels like fewer people care about email encryption today than they…
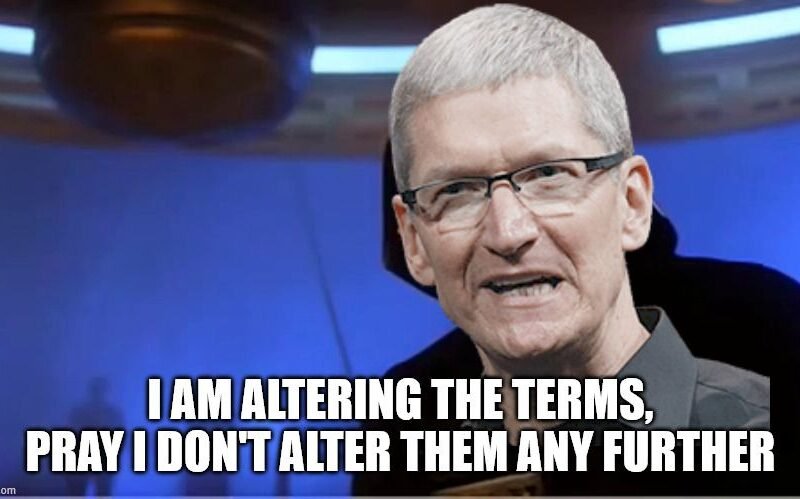
🔥 Check out this must-read post from Hacker News 📖 📂 Category: 💡 Here’s what you’ll learn: Summary: A major brick-and-mortar store sold an Apple Gift Card that Apple seemingly took offence to, and locked out my entire Apple ID, effectively bricking my devices and my iCloud Account, Apple Developer ID, and everything associated with it, and I have no recourse. Can you help? Email paris AT paris.id.au (and read on for the details). ❤️Here’s how Apple “Permanently” locked my Apple ID.I am writing this as a desperate measure. After nearly 30 years as a loyal customer, authoring technical books…
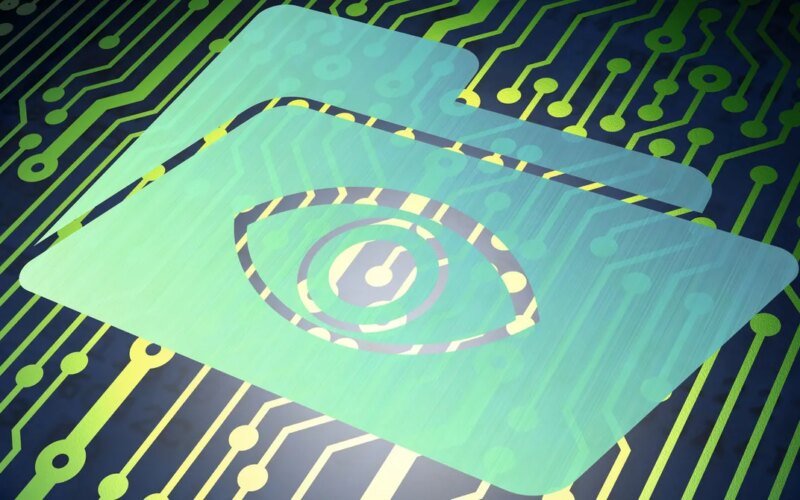
🚀 Read this awesome post from Hacker News 📖 📂 Category: 💡 Here’s what you’ll learn: When a privacy specialist at the legal response operations center of Charter Communications received an emergency data request via email on September 4 from Officer Jason Corse of the Jacksonville Sheriff’s Office, it took her just minutes to respond, with the name, home address, phone numbers, and email address of the “target.”But the email had not in fact come from Corse or anyone else at the Jacksonville Sheriff’s Office. It was sent by a member of a hacking group that provides doxing-as-a-service to customers…
💥 Read this must-read post from Hacker News 📖 📂 Category: 📌 Key idea: Your Complete Guide to AI-Powered Productivity Version 1.0 — December 2025 This collection contains 100 practical recipes for using Claude Code to automate, accelerate, and enhance your professional work. Each recipe provides step-by-step instructions, ready-to-use prompts, and real-world examples that you can apply immediately. Whether you're drafting emails, analyzing data, preparing presentations, or managing complex projects, there's a recipe here that will save you hours of work. Want all 200 recipes as ready-to-use slash commands? The Premium Collection includes 200 slash commands you can install in…
💥 Explore this must-read post from Hacker News 📖 📂 Category: 💡 Main takeaway: I hate sudo with a passion. It represents everything I find offensive about the modern Unix security model: like su, it must be a SUID binary to work it is monolithic: everything sudo does runs as root, there is no privilege separation it uses a non-declarative and non-hierarchical configuration format leading to forests of complex access-control policies and user errors due to lack of concision it supports plugins to extend the policy engine which run directly in the privileged SUID process I could go on, but…
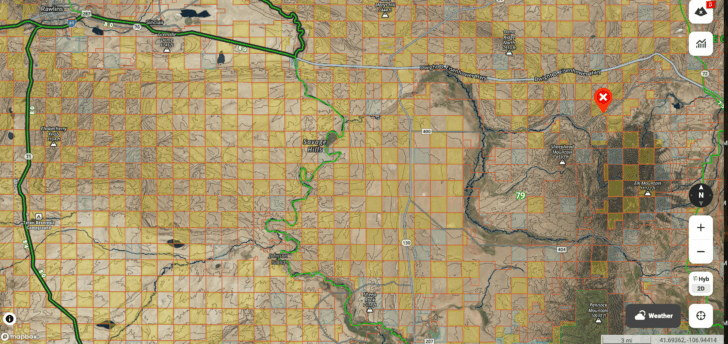
🔥 Check out this awesome post from Hacker News 📖 📂 Category: 📌 Here’s what you’ll learn: In 2019, hunters Brad Cape and Phil Yeomans were scouting for elk in southeast Wyoming when they came across a rocky peak that seemed perfect for elk hunting, a suspicion only heightened by its name: Elk Mountain. But finding a way onto Elk Mountain would turn out to be extremely difficult, and whether Brad and Phil succeeded would have lasting consequences for the future of land use everywhere in the U.S. because the single largest obstacle preventing the hunters from making it onto…

