💥 Explore this must-read post from Hacker News 📖 📂 Category: ✅ Key idea: Thesis: Castles created the modern state. Part 1 of the series explores the technology and why it was so important to medieval Europeans. It answers, “But why castles?”Text within this block will maintain its original spacing when published In any specific action, in any measure we may undertake, we always have the choice between the most audacious and the most careful solution. Some people think that the theory of war always advises the latter. That assumption is false. If the theory does advise anything, it is…

✨ Explore this insightful post from Hacker News 📖 📂 Category: 📌 Key idea: Note: Some patched versions are still being released to npm. If a version listed below is not yet available, please check back shortly. Two additional vulnerabilities have been identified in the React Server Components (RSC) protocol. These issues were discovered while security researchers examined the patches for React2Shell. Importantly, neither of these new issues allow for Remote Code Execution. The patch for React2Shell remains fully effective. These vulnerabilities originate in the upstream React implementation (CVE-2025-55183, CVE-2025-55184). This advisory tracks the downstream impact on Next.js applications using…

✨ Check out this awesome post from Hacker News 📖 📂 Category: ✅ Main takeaway: December 11, 2025 by The React Team Security researchers have found and disclosed two additional vulnerabilities in React Server Components while attempting to exploit the patches in last week’s critical vulnerability.These new vulnerabilities do not allow for Remote Code Execution. The patch for React2Shell remains effective at mitigating the Remote Code Execution exploit. The new vulnerabilities are disclosed as: These issues are present in the patches published last week. We recommend upgrading immediately due to the severity of the newly disclosed vulnerabilities. NoteIt’s common for…
💥 Read this must-read post from Hacker News 📖 📂 Category: ✅ Key idea:
My productivity app is a never-ending .txt file
By Jeff Huang, updated on 2022-03-21
The biggest transition for me when I started college was learning to get organized. There was a point when I couldn't just remember everything in my head. And having to constantly keep track of things was distracting me from whatever task I was doing at the moment.
So I tried various forms of todo lists, task trackers, and productivity apps. They were all discouraging because the…
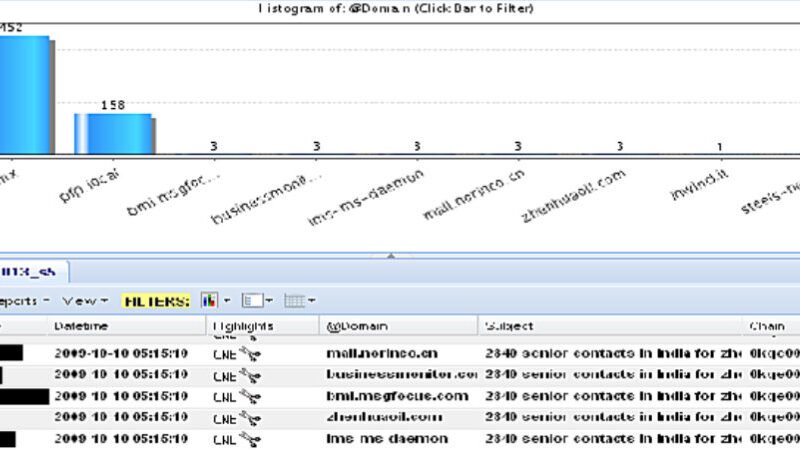
💥 Discover this insightful post from Hacker News 📖 📂 Category: 💡 Key idea: We are building a comprehensive archive and analysis project examining published documents leaked by Edward Snowden. Our methodology involves systematically reviewing each available document with particular attention to small details and information that has received little or no public attention since the initial 2013 disclosures. Throughout this process, we will publish posts highlighting interesting previously unreported findings. The main project will hopefully be complete and made public in mid-to-late 2026.This is Part 1 of our "Going Through Snowden Documents" series.Document: CNE Analysis in XKEYSCOREClassification: TOP SECRET//COMINT//REL…

🔥 Check out this must-read post from Hacker News 📖 📂 Category: ✅ Key idea: Google suspended a mobile app developer’s accounts after he uploaded AI training data to his Google Drive. Unbeknownst to him, the widely used dataset, which is cited in a number of academic papers and distributed via an academic file sharing site, contained child sexual abuse material. The developer reported the dataset to a child safety organization, which eventually resulted in the dataset’s removal, but he claims Google’s ban has been "devastating.”A message from Google said his account “has content that involves a child being sexually…
💥 Read this trending post from Hacker News 📖 📂 Category: 💡 Main takeaway: I’m sitting down to write this in a gap between jobs. The downtime is strange, like the world has stopped moving but my thoughts haven’t caught up. Other than replaying the shit that went down during the last six months – or to put it more bluntly, the reasons I left, I don’t quite know what to do with myself.What happened wasn’t unique. And that’s the part that bothers me most. It’s the same stuff I hear from friends, colleagues, people I trust across the industry.I know…
✨ Explore this awesome post from Hacker News 📖 📂 Category: 📌 Main takeaway: Explore Working in Cambridge, James Watson and Francis Crick discovered the double helix in early 1953, while Maurice Wilkins and Rosalind Franklin, researchers at King’s College London, were also trying to crack the structure. Franklin was about to leave King’s and DNA work all together, while Wilkins was preparing to focus his mind more closely on the problem once Franklin left. It’s widely believed that Watson and Crick stole Franklin’s data and that this enabled them to make their breakthrough.The idea can be traced back to…

💥 Discover this trending post from Hacker News 📖 📂 Category: 💡 Main takeaway: The Walt Disney Company on Thursday announced it will make a $1 billion equity investment in OpenAI and will allow users to make videos with its copyrighted characters on its Sora app.OpenAI launched Sora in September, and it allows users to create short videos by simply typing in a prompt. As part of the startup's new three-year licensing agreement with Disney, Sora users will be able make content with more than 200 characters across Disney, Marvel, Pixar and Star Wars starting next year. "The rapid advancement of artificial intelligence…

🔥 Read this insightful post from Hacker News 📖 📂 Category: 📌 Here’s what you’ll learn: Cymothoa exigua is a powerful little crustacean, with seven pairs of legs tipped with spines, which help her anchor into the fish's mouth. However, the first step in the process is to use her five sets of jaws modified with a variety of ice-pick-like tubes to puncture the fish's tongue and suck out the fish's blood. This process, by the way, is not thought to be very pleasant for the fish. As the isopod drains the fish's tongue of blood, the muscle itself atrophies…

