🔥 Discover this awesome post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: Sign up for the daily CJR newsletter. In May 2024, Daniel Ojukwu, a twenty-six-year-old reporter for the Foundation for Investigative Journalism, a Nigerian nonprofit, was grabbed off the streets of Lagos by armed police and bundled into a vehicle. For the next several days, he was held in a cell incommunicado—first in Lagos, and later in the federal capital, Abuja—without being told exactly what he’d been arrested for. “It was more of an abduction,” Ojukwu recalled recently, via WhatsApp. Finally, on the fourth day,…
🔥 Discover this awesome post from Hacker News 📖 📂 Category: 💡 Key idea: People rant about having to learn algorithmic questions for interviews. I get it — interview system is broken, but you ought to learn binary search at least. Anyways, yet again I came across a real life application of Algorithms. This time in the OG tool git. git bisect - Use binary search to find the commit that introduced a bug ref. And Leetcode wanted you to know it First Bad Version We use a monorepo at work. And people tend to make hundreds, if not thousands,…

🔥 Explore this insightful post from Hacker News 📖 📂 Category: 📌 Key idea: Starting this month, parking lots in South Korea with more than 80 spaces will be required to install solar canopies and carports. But, unlike similar laws that have been proposed in the US, this new law doesn’t just apply to new construction – existing lots will have to comply as well! South Korea’s Ministry of Trade, Industry and Energy announced in August that it has prepared an amendment to the Enforcement Decree of the Act on the Promotion of the Development, Use, and Diffusion of New and…
🚀 Check out this awesome post from Hacker News 📖 📂 Category: 📌 Key idea: ACM Classic: Reflections on Trusting Trust Reflections on Trusting TrustKen Thompson Reprinted from Communication of the ACM, Vol. 27, No. 8, August 1984, pp. 761-763. Copyright © 1984, Association for Computing Machinery, Inc. Also appears in ACM Turing Award Lectures: The First Twenty Years 1965-1985 Copyright © 1987 by the ACM press and Computers Under Attack: Intruders, Worms, and Viruses Copyright © 1990 by the ACM press. I copied this page from the ACM, in fear that it would someday turn stale. Introduction I thank…
💥 Check out this insightful post from Hacker News 📖 📂 Category: ✅ Key idea: GITHUB HUGGINGFACE MODELSCOPE SHOWCASEFrom Chatbot to Autonomous Agent#We are proud to present Tongyi DeepResearch, the first fully open‑source Web Agent to achieve performance on par with OpenAI’s DeepResearch across a comprehensive suite of benchmarks. Tongyi DeepResearch demonstrates state‑of‑the‑art results, scoring 32.9 on the academic reasoning task Humanity’s Last Exam (HLE), 43.4 on BrowseComp and 46.7 on BrowseComp‑ZH in extremely complex information‑seeking tasks, and achieving a score of 75 on the user‑centric xbench‑DeepSearch benchmark, systematically outperforming all existing proprietary and open‑source Deep Research agents.Beyond the model, we share a complete and battle‑tested methodology for creating such advanced agents. Our contribution details a novel data synthesis solution applied across the entire training pipeline, from Agentic Continual Pre‑training (CPT) and Supervised Fine‑Tuning (SFT) for cold‑starting, to the final Reinforcement Learning (RL) stage. For RL, we provide a full‑stack solution, including algorithmic innovations, automated data curation, and robust infrastructure. For inference, the vanilla ReAct framework showcases the model’s powerful intrinsic capabilities without any prompt engineering, while the advanced Heavy Mode (test‑time‑scaling) demonstrates the upper limits of its complex reasoning and planning potential.Continual Pre‑training and Post‑training Empowered by Fully Synthetic Data#Continual Pre‑training Data#We introduce Agentic CPT to deep research agent training, creating powerful agentic foundation models for post‑training. We propose AgentFounder, a systematic and scalable solution for large‑scale data synthesis that creates a data flywheel with data from the post‑training pipeline.Data Reorganization and Question Construction. We continuously collect data from various sources, including documents, publicly available crawled data, knowledge graphs, and historical trajectories and tool invocation records (e.g., search results with links). As shown in the figure, these diverse data sources are restructured into an entity‑anchored open‑world knowledge memory. Based on randomly sampled entities and their corresponding knowledge, we generate multi‑style (question,answer) pairs.Action Synthesis. Based on diverse problems and historical trajectories, we construct first‑order action synthesis data and higher‑order action synthesis data. Our method enables large‑scale and comprehensive exploration of the potential reasoning‑action space within offline environments, thereby thereby eliminating the need for additional commercial tool API calls. Specifically, for the higher‑order action synthesis, we remodel trajectories as multi‑step decision‑making processes to enhance the model’s decision‑making capabilities.Post-training Data#High-quality synthetic QA pairsWe develop an end‑to‑end solution for synthetic data generation. This fully automated process requires no human intervention to construct super‑human quality datasets, designed to push the boundaries of AI agent performance. Through long‑term exploration and iteration‑from early methods like reverse‑engineering QA pairs from clickstreams (WebWalker) to the more systematic graph‑based synthesis (WebSailor and WebSailor‑V2), then the formalized task modeling (WebShaper)‑our approach ensures both exceptional data quality and massive scalability, breaking through the upper limits of model capabilities.To address complex, high‑uncertainty questions, we synthesize web‑based QA data through a novel pipeline. The process begins by constructing a highly interconnected knowledge graph via random walks and isomorphic tables towards tabular data fusion from real‑world websites , ensuring a realistic information structure. We then sample subgraphs and subtables to generate initial questions and answers. The crucial step involves intentionally increasing difficulty by strategically obfuscating or blurring information within the question. This practical approach is grounded in a complete theoretical framework, where we formally model QA difficulty as a series of controllable “atomic operations” (e.g., merging entities with similar attributes) on entity relationships, allowing us to systematically increase complexity.To further reduce inconsistencies between the organized information structure and the reasoning structure of QA, enable more controllable difficulty and structure scaling of reasoning, we proposed a formal modeling of the information‑seeking problem based on set theory. With this formalization, we developed agents that expands the problem in a controlled manner, and minimizes reasoning shortcuts and structural redundancy, leading to further improved QA quality. Moreover, this formal modeling also allows for efficient verification of QA correctness, effectively addressing the challenge of validating synthetic information‑seeking data for post‑training.Furthermore, we have developed an automated data engine to scale up the creation of PhD‑level research questions. This engine begins with a multi‑disciplinary knowledge base, generating “seed” QA pairs that require multi‑source reasoning. Each seed then enters a self‑guided loop of “iterative complexity upgrades”, where a question‑crafting agent is equipped with a powerful toolset including web search, academic retrieval, and a Python execution environment. In each iteration, the agent expands knowledge boundaries, deepens conceptual abstraction, and even constructs computational tasks, creating a virtuous cycle where the output of one round becomes the more complex input for the next, ensuring a controllable and systematic escalation of task difficulty.Unleashing Agent Capabilities with Diverse Reasoning PatternTo bootstrap the model’s initial capabilities, we constructed a set of trajectories via rejection sampling, based on the ReAct and IterResearch frameworks (for details, see below). On one hand, ReAct, as a classic and foundational multi-turn reasoning format, instills rich reasoning behaviors and reinforces the model’s ability to adhere to structured formats.On the other hand, we introduce IterResearch, an innovative agent paradigm (detailed below). It unleashes the model’s full reasoning potential by…
💥 Discover this insightful post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: Many British consumers pay for 100% renewable electricity. But how much are they actually getting? The power sector has a dedicated system to track the generation and consumption of renewable power, and suppliers use it to back their green energy claims. But there's a problem. The rules allow suppliers to claim that summer power from solar farms is being used to cover winter evening power that came from gas plants. Your heating at 6pm in January? Almost certainly powered by fossil fuels, no matter…

✨ Explore this trending post from Hacker News 📖 📂 Category: 💡 Key idea: Over the past few months, I’ve noticed that an increasing number of replies to email that I’ve sent are “reactions”. I imagine that, to the sender, or to someone in the Microsoft ecosystem, they are handled a bit liked a “thumbs-up” or “heart” reaction to a Signal message. To me - as someone not in the Microsoft ecosystem - for each reaction, I get an email: like [person] reacted to your message: The “like” is alt-text. Because I don’t allow loading of remote content, I don’t…
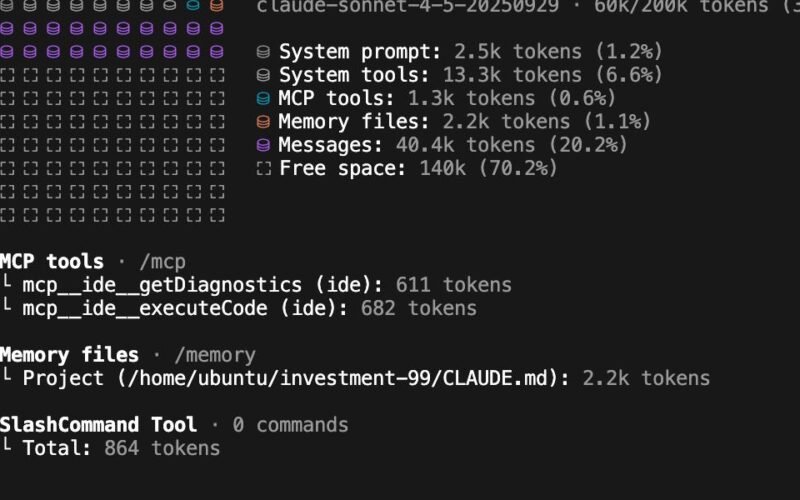
💥 Check out this awesome post from Hacker News 📖 📂 Category: 💡 Here’s what you’ll learn: I use Claude Code. A lot.As a hobbyist, I run it in a VM several times a week on side projects, often with --dangerously-skip-permissions to vibe code whatever idea is on my mind. Professionally, part of my team builds the AI-IDE rules and tooling for our engineering team that consumes several billion tokens per month just for codegen.The CLI agent space is getting crowded and between Claude Code, Gemini CLI, Cursor, and Codex CLI, it feels like the real race is between Anthropic…
🚀 Read this awesome post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: As our use of LLMs has changed from conversational chatbots and into integral decision-making components of complex systems, our inference approach must also evolve. The practice of "prompt engineering", in which precise wording is submitted to the LLM to elicit desired responses, has serious limitations. And so this is giving way to a more general practice of considering every token fed into the LLM in a way that is more dynamic, targeted, and deliberate. This expanded, more structured practice is what we now call…

🚀 Check out this insightful post from Hacker News 📖 📂 Category: 💡 Here’s what you’ll learn: Quick jumps to:– What digital alarm clocks before it were like– Why is the LM8560 so costs effective? The trick, how it works– Typical issues– Its weak point is also its strength– Its “hidden” functions– Some unwanted behaviors– That evil beep beep!– Limitations of use– Make a quartz clock / DC supply clock with the LM8560– Operating modes– Its relatives and predecessors– The Duplex display. A not versatile but clever solution– Not the best chip for electronics hobbyists– My alarm clocks– My first…