🚀 Explore this trending post from Hacker News 📖 📂 Category: ✅ Key idea: I'm impressed with the level of compatibility of the new memory-safe C/C++ compiler Fil-C (filcc, fil++). Many libraries and applications that I've tried work under Fil-C without changes, and the exceptions haven't been hard to get working. I've started accumulating miscellaneous notes on this page regarding usage of Fil-C. My selfish objective here is to protect various machines that I manage by switching them over to code compiled with Fil-C, but maybe you'll find something useful here too. Timings below are from a mini-PC named phoenix…
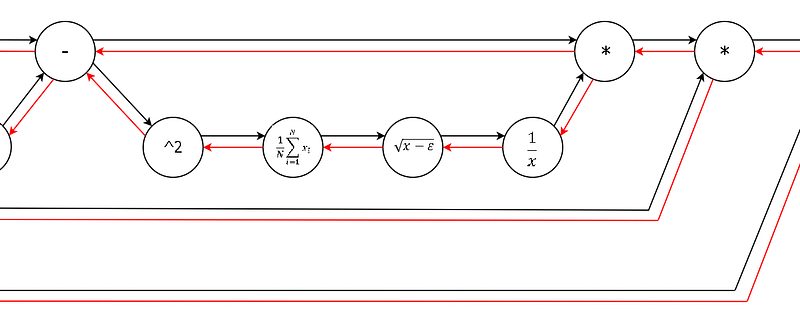
🚀 Check out this trending post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: When we offered CS231n (Deep Learning class) at Stanford, we intentionally designed the programming assignments to include explicit calculations involved in backpropagation on the lowest level. The students had to implement the forward and the backward pass of each layer in raw numpy. Inevitably, some students complained on the class message boards:“Why do we have to write the backward pass when frameworks in the real world, such as TensorFlow, compute them for you automatically?”This is seemingly a perfectly sensible appeal - if you’re…

🔥 Check out this insightful post from Hacker News 📖 📂 Category: 📌 Key idea: Unlock the Editor’s Digest for freeRoula Khalaf, Editor of the FT, selects her favourite stories in this weekly newsletter.Meta is planning to raise $25bn from a bond sale to help it pay for soaring artificial intelligence costs, even as the Big Tech group’s shares suffered one of their worst days ever over concerns that its spending is too high.The social media group had hired Citigroup and Morgan Stanley to raise up to $25bn in debt, ranging from five to 40 years in maturity, in what…
🚀 Explore this trending post from Hacker News 📖 📂 Category: 💡 Main takeaway: I’ve had a few conversations about async code recently (and not so recently) and seen some code that seems to make wrong assumptions about async, so I figured out it was time to have a serious chat about async, what it’s for, what it guarantees and what it doesn’t. Most of the code in this entry will be written with Python syntax (and often Python libraries), but with a few minor exceptions, we’ll be discussing concepts that are valid across languages. We all know about performance,…
💥 Read this trending post from Hacker News 📖 📂 Category: 📌 Main takeaway: High-performance lockless spsc/mpsc/mpmc channels. It supports async contexts, and communication between async and blocking contexts. The low level is based on crossbeam-queue. For the concept, please refer to the wiki. V1.0: Released in 2022.12 and used in production. V2.0: Released in 2025.6. Refactored the codebase and API by removing generic types from the ChannelShared type, which made it easier to code with. v2.1: Released in 2025.9. Removed the dependency on crossbeam-channel and implemented with a modified version of crossbeam-queue, which brings performance improvements for both async…

🚀 Explore this must-read post from Hacker News 📖 📂 Category: ✅ Key idea: Being: A reaction to Eliezer Yudkowsky and Nate Soares’s book “If anybody builds it everyone dies” which is getting a bit of media attentionI’ve known Eliezer Yudkowsky since the late 1990s. In 2000, he visited my AI company Webmind Inc. in New York City, where we were explicitly trying to build AGI alongside various commercial applications. His mission? To convince us to maybe stop. Or, failing that, to get us thinking really hard about AGI safety and how to make the AGI good for everyone.While he…
🚀 Discover this insightful post from Hacker News 📖 📂 Category: 💡 Key idea: The way we interact with the Internet is changing. Not long ago, ordering a pizza meant visiting a website, clicking through menus, and entering your payment details. Soon, you might just ask your phone to order a pizza that matches your preferences. A program on your device or on a remote server, which we call an AI agent, would visit the website and orchestrate the necessary steps on your behalf.Of course, agents can do much more than order pizza. Soon we might use them to buy…
✨ Discover this trending post from Hacker News 📖 📂 Category: 💡 Key idea: A web application that scans websites for potential API keys, secrets, and sensitive information leaks. This tool helps developers and security professionals identify and fix security vulnerabilities in their web applications. Referenced Project: Key detection patterns inspired by Keyleaksecret. Scans web pages for common secret patterns (API keys, passwords, tokens, etc.) Checks response headers for sensitive information Validates security headers User-friendly web interface Real-time scanning results Categorizes findings by severity Clone this repository: git clone <repository-url> cd keyleak-detector Create and activate a virtual environment (recommended): python…

🔥 Discover this trending post from Hacker News 📖 📂 Category: 📌 Key idea:
Welcome! Visopsys is an alternative operating system for PC compatible computers. In development since 1997, this system is small, fast, and open source. It features a simple but functional graphical interface, pre-emptive multitasking, and virtual memory. Though it attempts to be compatible in a number of ways, Visopsys is not a clone of any other operating system. You can demo the distribution from a “live” USB stick, CD/DVD, or floppy disk … (read more). Features of Visopsys Small & fast Graphical user interface Fully…

💥 Check out this insightful post from Hacker News 📖 📂 Category: 💡 Key idea: Sailfish OS’s heritage lies in Nokia times, especially in the MeeGo operating system. Prior to 2011 Nokia and Intel had a vision of an open mobile operating system. Together they invested around 1 billion USD to the project and created an open source based operating system called MeeGo, which was used as a basis for several devices, such as the iconic Nokia N9. Although the Nokia N9 became the beacon of open source operating systems, Nokia decided to end the project and chose instead to…
