✨ Discover this awesome post from Hacker News 📖 📂 Category: 💡 Main takeaway: Chris VallanceSenior technology reporterGetty ImagesPornhub says the number of UK visitors to its website is down 77% compared with July, when more rigorous age checks for sexually explicit sites were introduced under the Online Safety Act.It claims sites that are ignoring the new requirements are benefiting.The BBC has not been able to independently verify Pornhub's claim - however, data from Google shows searches for the site have decreased by almost half since the law came into effect.This could be a consequence of people reducing their porn…

✨ Read this insightful post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: Last week, as ICE raids ramped up in New York, city residents set about resisting in the ways they had available: confronting agents directly on sidewalks, haranguing them as they processed down blocks, and recording them on phone cameras held aloft. Relentless documentation has proved something of an effective tool against President Donald Trump’s empowerment of ICE; agents have taken to wearing masks in fear of exposure, and the proliferation of imagery showing armed police and mobilized National Guard troops in otherwise calm cities…
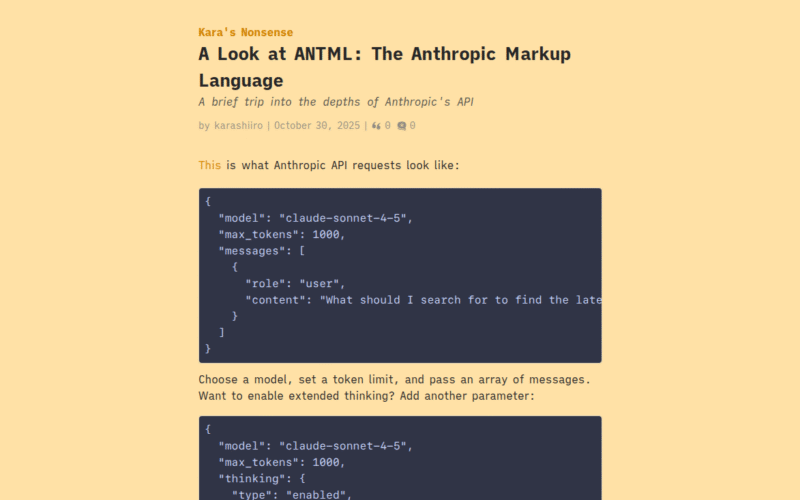
🔥 Read this trending post from Hacker News 📖 📂 Category: 📌 Here’s what you’ll learn: This is what Anthropic API requests look like:⚡Choose a model, set a token limit, and pass an array of messages. Want to enable extended thinking? Add another parameter:🔥Now, how does the API know when the model is thinking? Maybe there's some special output channel, or behind-the-scenes prompting in a separate context, or something?As it turns out, the model just wraps its thinking in some special XML tags:UserGet OIDC Test auth info.AssistantThe user is asking me to get OIDC Test auth info. Looking at the…
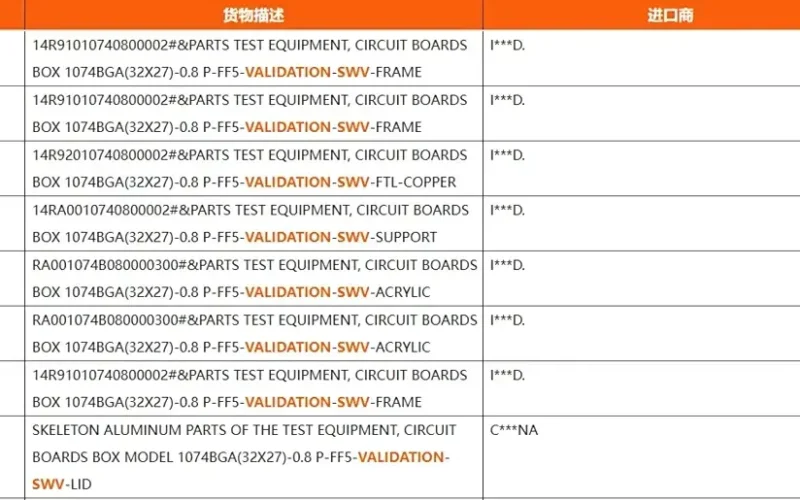
🚀 Discover this awesome post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: AMD is expanding its processor portfolio beyond the x86 architecture with its first ARM-based APU, internally known as “Sound Wave.” The chip’s existence was uncovered through customs import records, confirming several details about its design and purpose. Built with a BGA-1074 package measuring 32 mm × 27 mm, the processor fits within standard mobile SoC dimensions, making it suitable for thin and light computing platforms. It employs a 0.8 mm pitch and FF5 interface, replacing the FF3 socket previously used in Valve’s Steam handheld…
🔥 Discover this awesome post from Hacker News 📖 📂 Category: ✅ Main takeaway: The best way to write code is to write no code at all. Writing code that does nothing is great, but sometimes you still want your code to do something. This package allows you to write nothing, and still have your code do something. TipIt is highly recommended to use a virtual environment for proper installation of the no.pth file. python -m pip install git+https://github.com/lemonyte/no-code Python 3.10 or a newer version is required. This package is intended to be used as a command-line tool. ImportantMake sure…
🔥 Discover this trending post from Hacker News 📖 📂 Category: 💡 Here’s what you’ll learn: Chromium Browser DoS Attack via document.title Exploitation Brash is a critical vulnerability in Blink, the rendering engine that powers Google's Chromium-based browsers. It allows any Chromium browser to collapse in 15-60 seconds by exploiting an architectural flaw in how certain DOM operations are managed. The attack vector originates from the complete absence of rate limiting on document.title API updates. This allows injecting millions of DOM mutations per second, and during this injection attempt, it saturates the main thread, disrupting the event loop and causing…
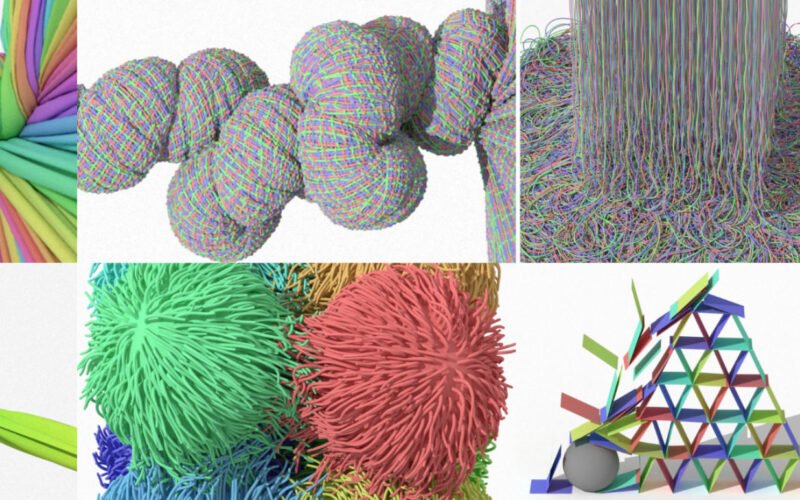
🚀 Check out this insightful post from Hacker News 📖 📂 Category: 💡 Key idea: A contact solver for physics-based simulations involving 👚 shells, 🪵 solids and 🪢 rods. All made by ZOZO. 💪 Robust: Contact resolutions are completely penetration-free. No snagging intersections. ⏲ Scalable: An extreme case includes beyond 150M contacts. Not just one million. 🚲 Cache Efficient: All on the GPU runs in single precision. No double precision. 🥼 Inextensible: Cloth never extends beyond very strict upper bounds, such as 1%. 📐 Physically Accurate: Our deformable solver is driven by the Finite Element Method. ⚔️ Highly Stressed: We…
💥 Check out this must-read post from Hacker News 📖 📂 Category: 📌 Here’s what you’ll learn: (a) On MMLU-Pro (4k context length), Kimi Linear achieves 51.0 performance with similar speed as full attention. On RULER (128k context length), it shows Pareto-optimal performance (84.3) and a 3.98x speedup. (b) Kimi Linear achieves 6.3x faster TPOT compared to MLA, offering significant speedups at long sequence lengths (1M tokens). Kimi Linear is a hybrid linear attention architecture that outperforms traditional full attention methods across various contexts, including short, long, and reinforcement learning (RL) scaling regimes. At it's core is Kimi Delta Attention…

💥 Discover this must-read post from Hacker News 📖 📂 Category: ✅ Main takeaway: Let’s talk about how the cochlea computes!The tympanic membrane (eardrum) is vibrated by changes in air pressure (sound waves). Bones in the middle ear amplify and send these vibrations to the fluid-filled, snail-shaped cochlea. Vibrations travel through the fluid to the basilar membrane, which remarkably performs frequency separation: the stiffer, lighter base resonates with high frequency components of the signal, and the more flexible, heavier apex resonates with lower frequencies. Between the two ends, the resonant frequencies decrease logarithmically in space.Resonant frequencies of the basilar membrane.…

💥 Read this trending post from Hacker News 📖 📂 Category: 📌 Key idea: Denmark’s justice minister on Thursday said he will no longer push for an EU law requiring the mandatory scanning of electronic messages, including on end-to-end encrypted platforms. Earlier in its European Council presidency, Denmark had brought back a draft law which would have required the scanning, sparking an intense backlash. Known as Chat Control, the measure was intended to crack down on the trafficking of child sex abuse materials (CSAM). After days of silence, the German government on October 8 announced it would not support the…

