🔥 Read this must-read post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: Follow @popovicu94 If you carefully read the Linux kernel docs, you will find an interesting statement: Linux has also been ported to itself. You can now run the kernel as a userspace application - this is called UserMode Linux (UML). Today, we’ll explore how you can start an unconventional VM by running a Linux kernel as a process within the Linux kernel itself. This approach doesn’t require installing virtualization software like QEMU, nor does it need root privileges, which opens up some intriguing possibilities.…
✨ Discover this trending post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: Background. Clearview AI is a US company that scrapes the internet and adds all of the faces it can find in photos and videos to its database. It claims to have collected more than 60 billion photos. This allows customers of Clearview AI to identify people by uploading a photo and obtaining other pictures of the same person, including links, the name of a subpage of a website and other meta data. The company originally tried to operate largely under the radar but the New York…
🚀 Read this must-read post from Hacker News 📖 📂 Category: ✅ Main takeaway: You’ve probably seen it in analytics dashboards, server logs, or privacy documentation: IP addresses with their last octet zeroed out. 192.168.1.42 becomes 192.168.1.0. For IPv6, maybe the last 64 or 80 bits are stripped. This practice is widespread, often promoted as “GDPR-compliant pseudonymization,” and implemented by major analytics platforms, log aggregation services, and web servers worldwide. There’s just one problem: truncated IP addresses are still personal data under GDPR. If you’re using IP address truncation thinking it makes data “anonymous” or “non-personal,” you’re creating a false…
✨ Discover this must-read post from Hacker News 📖 📂 Category: 💡 Main takeaway: Why I Built This My team needed to choose a framework for an upcoming app. The requirements were clear: it had to work well on mobile. Not “acceptable on mobile,” but actually good. We’re building tools for real estate agents working in the field: open houses, parking lots, spotty cellular signals. When someone’s standing in front of a potential buyer trying to look professional, a slow-loading app isn’t just an annoyance. It’s a liability. I started with what seemed like a reasonable comparison: Next.js (our current…
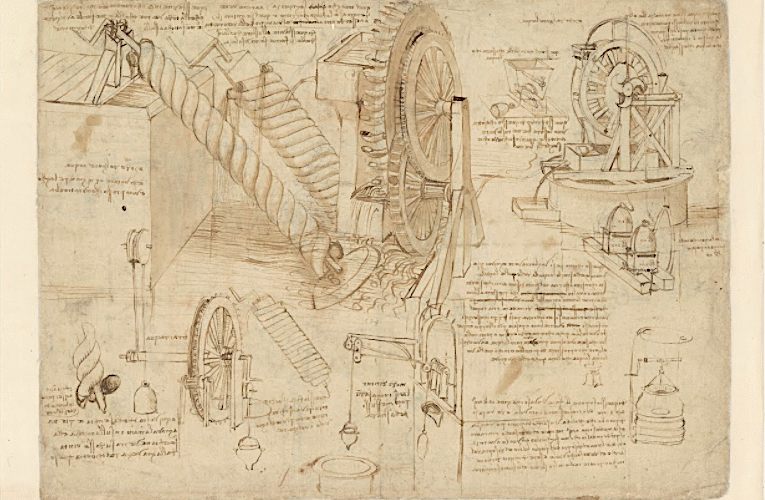
🔥 Read this awesome post from Hacker News 📖 📂 Category: 📌 Main takeaway: No historical figure better fits the definition of “Renaissance man” than Leonardo da Vinci, but that term has become so overused as to become misleading. We use it to express mild surprise that one person could use both their left and right hemispheres equally well. But in Leonardo’s day, people did not think of themselves as having two brains, and the worlds of art and science were not so far apart as they are now. That Leonardo was able to combine fine arts and fine engineering…
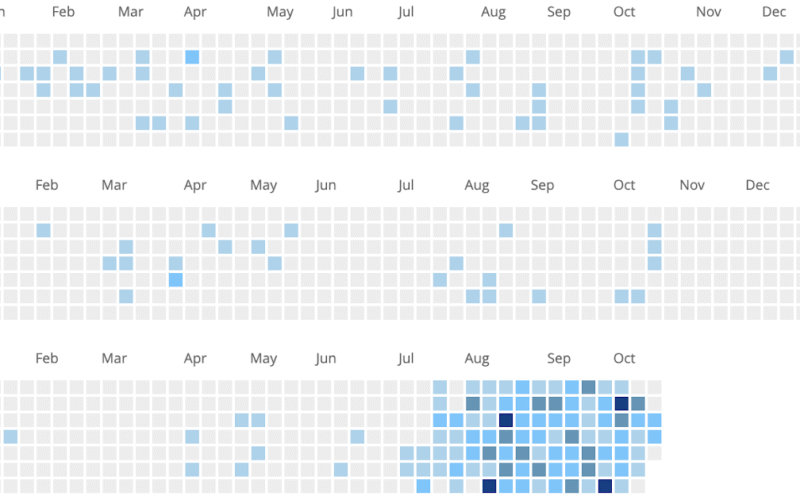
🔥 Check out this awesome post from Hacker News 📖 📂 Category: 💡 Here’s what you’ll learn: Personal Science Could this be the world’s most advanced AI journal and projects app? You Decide Pricing Dlog is free for the first 14 days, and comes with 10,000 free tokens. The price is then 1.99 per month, plus tokens. If you purchase within 24 hours you get 1 million free tokens (normally 5.99 / million). Quick Start Video Harness personal strengths and understand the drivers behind your productivity and wellbeing. Built on a decade of research. Dlog learns your personality, standards and…
🚀 Discover this must-read post from Hacker News 📖 📂 Category: 💡 Key idea: Over the past three months, a team of experienced, like-minded engineers and I have been building something really cool within Amazon Bedrock. While I'm pretty excited about what we are building, there is another unique thing about our team - most of our code is written by AI agents such as Amazon Q or Kiro. Before you roll your eyes: no, we're not vibe coding. I don't believe that's the right way to build robust software.Instead, we use an approach where a human and AI agent…
🔥 Explore this must-read post from Hacker News 📖 📂 Category: 💡 Here’s what you’ll learn: A Python tool for scanning MCP (Model Context Protocol) servers and tools for potential security vulnerabilities. The MCP Scanner combines Cisco AI Defense inspect API, YARA rules and LLM-as-a-judge to detect malicious MCP tools. The MCP Scanner provides a comprehensive solution for scanning MCP servers and tools for security vulnerabilities. It leverages three powerful scanning engines (Yara, LLM-as-judge, Cisco AI Defense) that can be used together or independently. The SDK is designed to be easy to use while providing powerful scanning capabilities, flexible authentication…

💥 Explore this insightful post from Hacker News 📖 📂 Category: 💡 Here’s what you’ll learn: oss-sec mailing list archives From: Moritz Mühlenhoff Date: Mon, 27 Oct 2025 19:21:54 +0000 On Mon, Oct 27, 2025 at 09:34:03AM -0700, Alan Coopersmith wrote: Among the new CVE's published this weekend were these from the VulDB CNA: For all three bugs, the documented "exploit" requires "Replace the default configuration file (/etc/dnsmasq.conf) with the provided malicious file." and if you can replace the server's configuration file you don't need to play games with putting invalid contents in to break the parser, but can simply…
🚀 Read this must-read post from Hacker News 📖 📂 Category: ✅ Main takeaway: Have you noticed that quite a few people are looking for technical cofounders or CTOs right now? I, for one, get a surprising amount of these queries; most of them along the lines of “hey, I have this vibe-coded app, would you like to make it production-ready”. I have sort of a profile for these people. Think someone who knows their business but has always lacked the technical skills to make their ideas happen — a legal counsel, perhaps, or an account manager. Why would these…