🚀 Read this must-read post from Hacker News 📖 📂 Category: 💡 Key idea: A shared commitment to advancing the future of systems programming and reliable distributed software Synadia and TigerBeetle have together pledged a combined $512,000 USD to the Zig Software Foundation (ZSF) over the next two years, demonstrating a shared belief in Zig’s potential to shape the next era of high-performance, reliable, and maintainable software. Synadia’s Mission: Connecting Everything At Synadia, we help some of the world’s largest enterprises design and scale innovative architectures across cloud regions, cloud providers, and all the way to the far edge. Often…
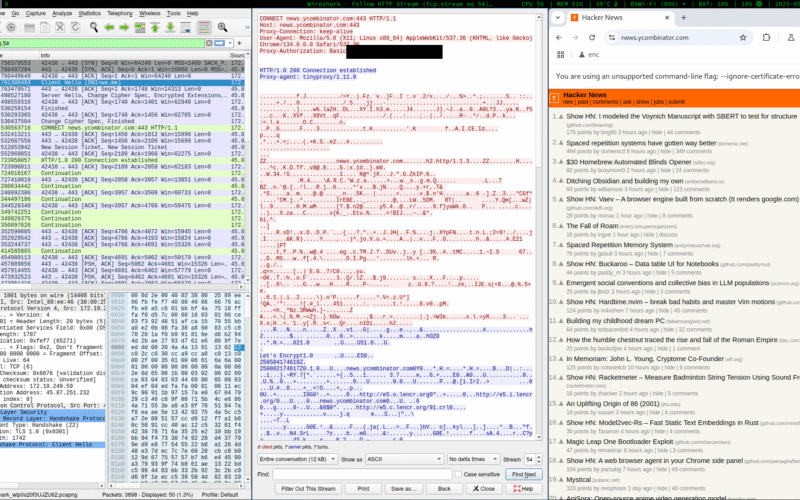
🚀 Discover this must-read post from Hacker News 📖 📂 Category: 📌 Here’s what you’ll learn: 2025-06-01 I was recently flying between HKG & LHR via British Airways. I’d done the same flight back in 2023, and remember relying on the in-flight entertainment for the 14 hour journey. However, this time on my way to London, they had an interesting offer: Free WiFi for “Messaging”, for members of “The British Airways Club”. I was pretty sure I wasn’t a member of any sort of club (I’m only flying economy anyway); but turns out this is just the name of their…
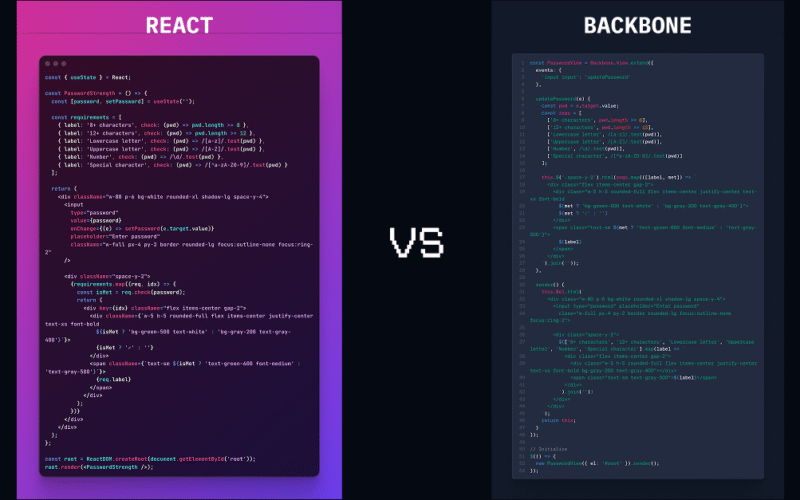
✨ Check out this insightful post from Hacker News 📖 📂 Category: 📌 Main takeaway: 15 Years of Progress Look at the two implementations above. The code is roughly the same length. They do exactly the same thing. One was written with a framework from 2010, the other with a framework that's had countless developer hours and a massive ecosystem behind it for over a decade. The interesting part is not how much better React is—it's how little progress we've actually made. The Illusion of Simplicity React looks cleaner. It reads better at first glance. But that readability comes at…
💥 Read this insightful post from Hacker News 📖 📂 Category: 📌 Key idea: Classes teach you all about advanced topics within CS, from operating systems to machine learning, but there’s one critical subject that’s rarely covered, and is instead left to students to figure out on their own: proficiency with their tools. We’ll teach you how to master the command-line, use a powerful text editor, use fancy features of version control systems, and much more! Students spend hundreds of hours using these tools over the course of their education (and thousands over their career), so it makes sense to…
✨ Read this trending post from Hacker News 📖 📂 Category: 💡 Main takeaway: Fast TypeScript Analyzer FTA (Fast TypeScript Analyzer) is a super-fast TypeScript static analysis tool written in Rust. It captures static information about TypeScript code and generates easy-to-understand analytics that tell you about complexity and maintainability issues that you may want to address. FTA uses swc (opens in a new tab) to parse your code then runs various analytical routines against it to understand how complex and maintainable it is likely to be. JavaScript code is also supported. ⚡FTA is fast: on typical hardware, it can analyze…
💥 Check out this awesome post from Hacker News 📖 📂 Category: 📌 Here’s what you’ll learn: When Ken Thompson won the Turing Award jointly with Dennis Ritchie for their work in UNIX, he was expected like other Turing winners to write a paper that would be published in the ACM Computer Journal. What he ended up submitting was a paper about "the cutest program [he] ever wrote"-- a sneaky undetectable self-reproducing "Trojan horse" backdoor in the C compiler that would allow him to log into affected machines as any user. Table of Contents Thompson didn't want to write about…

🚀 Discover this must-read post from Hacker News 📖 📂 Category: 📌 Key idea: European police forces have arrested seven people and dismantled a large-scale cybercrime-as-a-service operation that saw almost 50 million fake online accounts created across social media and communications platforms for fraud purposes.
Seized SIM boxes in Latvia
Latvian Police/Europol
The coordinated takedown, codenamed Operation SIMCARTEL, took place on October 10 in Latvia, as part of a joint investigation by police in the Baltic nation, Austria, Estonia and Finland. Five Latvian nationals and two additional suspects were arrrested by police. In the raid, authorities seized 1200…

✨ Check out this trending post from Hacker News 📖 📂 Category: ✅ Key idea: A lot of people say AI will make us all “managers” or “editors”…but I think this is a dangerously incomplete view! Personally, I’m trying to code like a surgeon. A surgeon isn’t a manager, they do the actual work! But their skills and time are highly leveraged with a support team that handles prep, secondary tasks, admin. The surgeon focuses on the important stuff they are uniquely good at. My current goal with AI coding tools is to spend 100% of my time doing stuff…

✨ Discover this insightful post from Hacker News 📖 📂 Category: ✅ Here’s what you’ll learn: As iOS 26 is being rolled out, our team noticed a particular change in how the operating system handles the shutdown.log file: it effectively erases crucial evidence of Pegasus and Predator spyware infections. This development poses a serious challenge for forensic investigators and individuals seeking to determine if their devices have been compromised at a time when spyware attacks are becoming more common.The Power of the shutdown.logFor years, the shutdown.log file has been an invaluable, yet often overlooked, artifact in the detection of iOS…
🔥 Check out this insightful post from Hacker News 📖 📂 Category: 📌 Here’s what you’ll learn: What makes an effective principal engineer or scientist? Here, I’ve distilled what I’ve observed from role models and quoted some of their advice below. While my perspective is naturally Amazon-centric, these ideas should also apply to most principal tech IC roles. As always, use your best judgment and assess if this advice applies to you and your situation. • • • 1. Different principals will have different flavors. Some dive deep in one space while others excel at horizontal influence. Some are technical…

