💥 Check out this awesome post from Hacker News 📖 📂 **Category**: ✅ **What You’ll Learn**: Abstract Tire Pressure Monitoring System (TPMS) transmissions of modern cars are sent over the air in clear text
and entail a unique identifier that does not change over very long periods of time. In this work, we investigate the privacy implications for car owners of this design choice by collecting and analyzing TPMS transmissions from a network of low-cost spectrum receivers that we deploy along the road over a period of 10 weeks. Our measurement study comprises data from 12 verified cars, but malicious…

✨ Check out this insightful post from Hacker News 📖 📂 **Category**: ✅ **What You’ll Learn**: US President Donald Trump had been sending mixed signals about whether he planned to attack Iran, preparing for war while saying he favors dialogue. The United States has moved military assets closer to the Middle East over the past few weeks, raising concerns that the prospects of war were growing. Trump said on January 22 that the US had “an armada” moving toward Iran “just in case,” adding that while he would rather not “see anything happen,” the US is watching Iran “very closely.”…

🔥 Explore this must-read post from Hacker News 📖 📂 **Category**: ✅ **What You’ll Learn**: In the United States, we are losing our fondness for cash. As in many other countries, cards and other types of electronic payments now dominate everyday commerce. To some, this is a loss. Cash represented a certain freedom from intermediation, a comforting simplicity, that you just don't get from Visa. It's funny to consider, then, how cash is in fact quite amenable to automation. Even Benjamin Franklin's face on a piece of paper can feel like a mere proxy for a database transaction. How different…
🔥 Check out this trending post from Hacker News 📖 📂 **Category**: ✅ **What You’ll Learn**: Introduction#For several years, I’ve been looking to manage my system configuration “As-code” to ensure reproducibility and consistency across my environments. The primary goal was to install my work laptop, but I also need to install Linux servers (without Kubernetes, so Talos isn’t an option).Initially, I used Packer to generate a virtual machine image, which I would then clone onto the disk of the machine I wanted to configure. It worked very well for server templates, but for a dev machine, it was a bit…
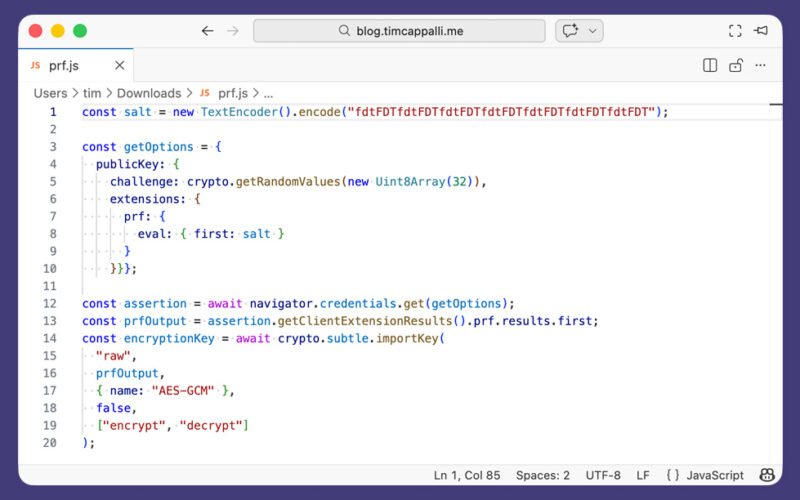
🚀 Explore this must-read post from Hacker News 📖 📂 **Category**: ✅ **What You’ll Learn**: Why am I writing this today? Because I am deeply concerned about users losing their most sacred data.Over the past year or two, I’ve seen many organizations, large and small, implement passkeys (which is great, thank you!) and use the PRF (Pseudo-Random Function) extension to derive keys to protect user data, typically to support end-to-end encryption (including backups). I’ve also seen a number of influential folks and organizations promote the use of PRF for encrypting data.The primary use cases I’ve seen implemented or promoted so…

🚀 Explore this awesome post from Hacker News 📖 📂 **Category**: 💡 **What You’ll Learn**: The Pentagon is seen from an airplane, Monday, Feb. 2, 2026, in Washington. Julia Demaree Nikhinson/Associated Press hide caption toggle caption Julia Demaree Nikhinson/Associated Press President Trump ordered the U.S. government to stop using the artificial intelligence company Anthropic's products and the Pentagon moved to designate the company a national security risk on Friday, in a sharp escalation of a high-stakes fight over the military's use of AI. The twin decisions cap an acrimonious dispute between Anthropic and the Pentagon over whether the company could…

✨ Read this insightful post from Hacker News 📖 📂 **Category**: ✅ **What You’ll Learn**: Earlier today, Secretary of War Pete Hegseth shared on X that he is directing the Department of War to designate Anthropic a supply chain risk. This action follows months of negotiations that reached an impasse over two exceptions we requested to the lawful use of our AI model, Claude: the mass domestic surveillance of Americans and fully autonomous weapons.We have not yet received direct communication from the Department of War or the White House on the status of our negotiations.We have tried in good faith…

🚀 Discover this insightful post from Hacker News 📖 📂 **Category**: ✅ **What You’ll Learn**: Frequently Asked Questions Have you thought about broadening the requests to be more comprehensive? The goal of this letter is to find common ground. The signatories likely have a diverse set of views. The current situation with the DoW is so clear-cut that it can bring together a very broad coalition. Signing this letter doesn't mean you think it's the only thing that needs to be done, just that you agree with the bottom line. Who is behind this? This letter was organized by a…

🚀 Read this trending post from Hacker News 📖 📂 **Category**: ✅ **What You’ll Learn**: There is a lot of energy right now around sandboxing untrusted code. AI agents generating and executing code, multi-tenant platforms running customer scripts, RL training pipelines evaluating model outputs—basically, you have code you did not write, and you need to run it without letting it compromise the host, other tenants, or itself in unexpected ways.The word “isolation” gets used loosely. A Docker container is “isolated.” A microVM is “isolated.” A WebAssembly module is “isolated.” But these are fundamentally different things, with different boundaries, different attack…
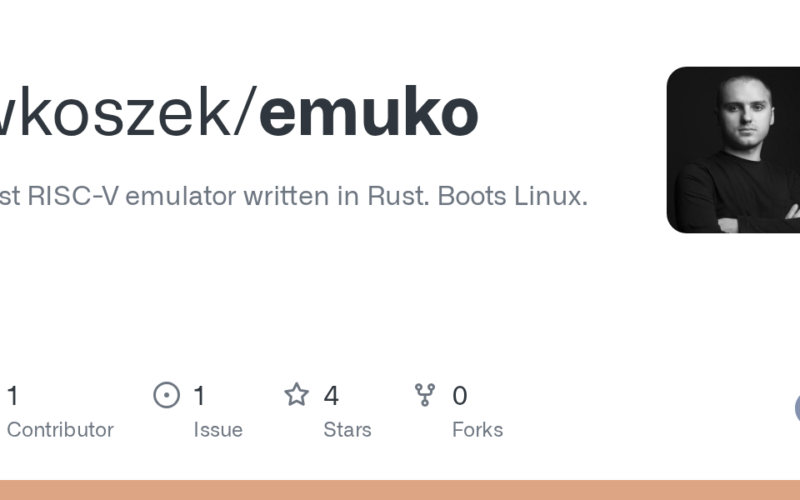
🔥 Explore this awesome post from Hacker News 📖 📂 **Category**: 💡 **What You’ll Learn**: Fast RISC-V emulator written in Rust. Boots Linux. emuko.dev RV64IMAFDC with M/S/U privilege levels and Sv39 virtual memory JIT compilation for ARM64 and x86_64 hosts (adaptive selection) Full Linux boot with BusyBox userland and interactive shell Snapshot/restore for saving and resuming full machine state Daemon mode with HTTP API and live UART command injection Differential checker to validate JIT against interpreter Peripherals: UART 16550, CLINT, PLIC, SBI 1.0, FDT generation Single dependency (zstd), pure Rust RISC-V Emulator Comparison (emuko vs others) This is a direct…
