🔥 Discover this must-read post from TechCrunch 📖
📂 Category: Security,Amnesty International,cybersecurity,government spyware,Intellexa,mercenary spyware,Predator,privacy,Spyware,surveillance,Tal Dilian
📌 Key idea:
Spyware maker Intellexa has gained remote access to some of its government clients’ surveillance systems, giving company employees the ability to see the personal data of people whose phones were hacked using the Predator spyware, according to new evidence published by Amnesty International.
On Thursday, Amnesty International and a coalition of media partners, including the Israeli newspaper Haaretz, the Greek news site Inside Story, and the Swiss outlet Inside IT, published a series of reports based on leaked materials from Intellexa, including internal company documents, sales and marketing materials, and training videos.
Perhaps the most surprising revelation is that people who work at Intellexa can remotely access the monitoring systems of at least some of its customers via TeamViewer, an off-the-shelf tool that allows users to connect to other computers over the Internet.
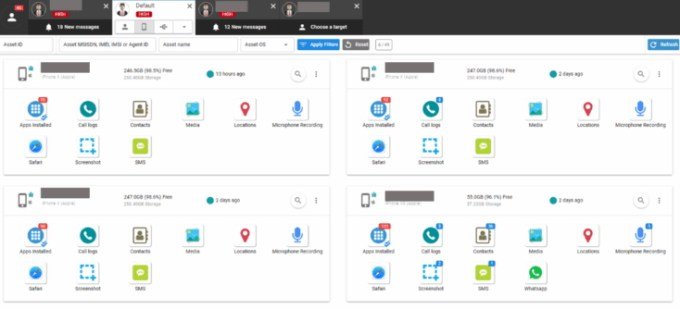
The remote access is shown in a leaked training video that reveals distinct parts of the Predator spyware system, including the dashboard, as well as “the storage system containing images, messages and all other surveillance data collected from victims of the Predator spyware,” Amnesty International wrote in its report. (Amnesty International published screenshots taken from the video, but not the full video.)
The leaked video shows “live” hit attempts by Predators “against real targets,” based on detailed information “from at least one hit attempt against a target in Kazakhstan,” the nonprofit researchers wrote. The video contains the infection URL, the target’s IP address, and the software versions of the target’s phone.
Companies that sell spyware to government agencies, such as NSO Group and the now-defunct Hacking Team, have long maintained that they can never access the data of their clients’ targets, nor their clients’ systems. There are several reasons for this.
From the point of view of spyware makers, they do not want to incur potential legal liability if their customers use spyware illegally. Spyware makers like to say that once their spyware is sold, customers bear full responsibility for its use. From the perspective of government agents, they do not want to reveal sensitive details of their investigations, such as the names, locations, and personal data of targets, to a private company that may be based abroad.
In other words, this kind of remote access is not “normal” at all, Paolo Lisi, CEO of spyware maker Memento Labs, told TechCrunch when contacted for this story to inquire from the spyware maker’s perspective. “no [government] He said the agency would accept that.
That’s why Lezzi was skeptical that the leaked training video showed access to an actual agent’s live monitoring system. Perhaps, he assumed, this was training material showing an experimental environment. The CEO also said that some customers have asked Memento Labs to access their systems, but the company only accepts the offer if it is necessary to resolve technical issues. However, he said, “They enable us to access TeamViewer for the time necessary and under their supervision we step in and leave.”
Contact us
Do you have more information about Intellexa? Or other spyware makers? From a non-work device, you can contact Lorenzo Franceschi-Bicchierai securely on Signal at +1 917 257 1382, via Telegram and Keybase @lorenzofb, or email.
However, Amnesty International is convinced that the leaked video shows access to the Predator’s live surveillance systems.
“One of the staff members on the training call asked if it was a sandbox, and the trainer confirmed it was a live system for customers,” said Doncha O Serbhil, head of Amnesty International’s security lab, which conducted technical analysis of the leaked material and investigated several cases of Predator infections.
The claim that Intellexa employees have a clear view of who their clients are spying on has raised concerns from Amnesty International about security and privacy.
“These findings can only heighten the concerns of potential surveillance victims,” the nonprofit wrote in the report. “Not only is their most sensitive data vulnerable to the government or other spyware agents, but their data is at risk to a foreign surveillance company, which has obvious problems keeping their confidential data securely stored.”
Intellexa could not be reached for comment. A lawyer speaking on behalf of Intellexa founder Tal Dilian told Haaretz that Dilian “did not commit any crime and did not operate any electronic system in Greece or anywhere else.”
Dillian is one of the most controversial people in the world of government spyware. A spyware industry veteran previously told TechCrunch that Dillian “moves like an elephant in a crystal store,” meaning he made little effort to hide his activities.
“In that particular space of spyware vendors, you have to be very balanced and attentive… but he didn’t care,” the person said.
In 2024, the US government announced sanctions against Tal Dalian and one of his business partners, Sarah Alexandra Faisal Hamo. In that case, the US Treasury Department imposed sanctions based on allegations that the Intellexa spyware had been used against Americans, including US government officials, journalists, and policy experts. The sanctions make it illegal for US companies and citizens to have any business relationship with Dillian and Hamo.
It was the first time that the US government, which took action against NSO Group spyware, targeted a specific person involved in the industry.
In his response to Haaretz, Dillian accused journalists of being “useful idiots” in a “coordinated campaign” to harm him and his company, which was “fed to the Biden administration.”
⚡ What do you think?
#️⃣ #Intellexa #sanctioned #spyware #maker #direct #access #victims #government #spying #researchers
🕒 Posted on 1764873201